Bypass
- Change the HTTP Verb.
- you can check the allowed http methods using
OPTION
- Then, can try one of the methods to check if it responds differently.
- This is due to
Insecure COnfig
IMPORTANT
- Change
POST request to a GET request with those parameters
Bypass Filters
- give input and press 'Enter'
- check that the file is created
- give input for command injection -
test;
- notice that the app responds with
malicious request detected.
- It can be that the security filter is only applied for a specific http method.
- changing the http method, the app fulfills the request.
- Now, we can do command injection by changing the GET request to a POST request.
- This is due to
Insecure Coding
Prevention
- most modern web servers, including
Apache, Tomcat, and ASP.NET have this.
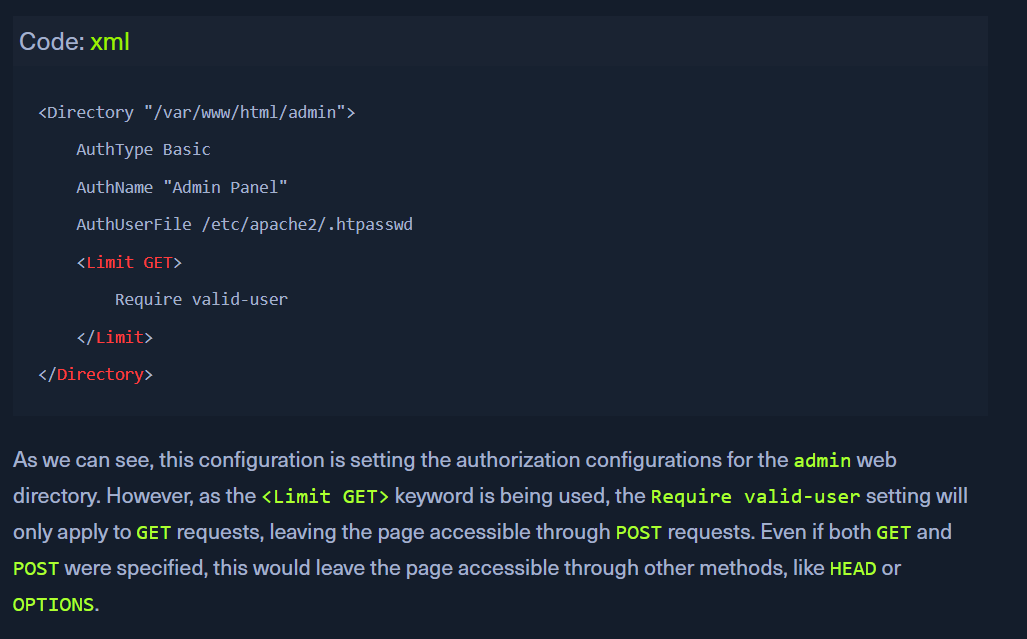
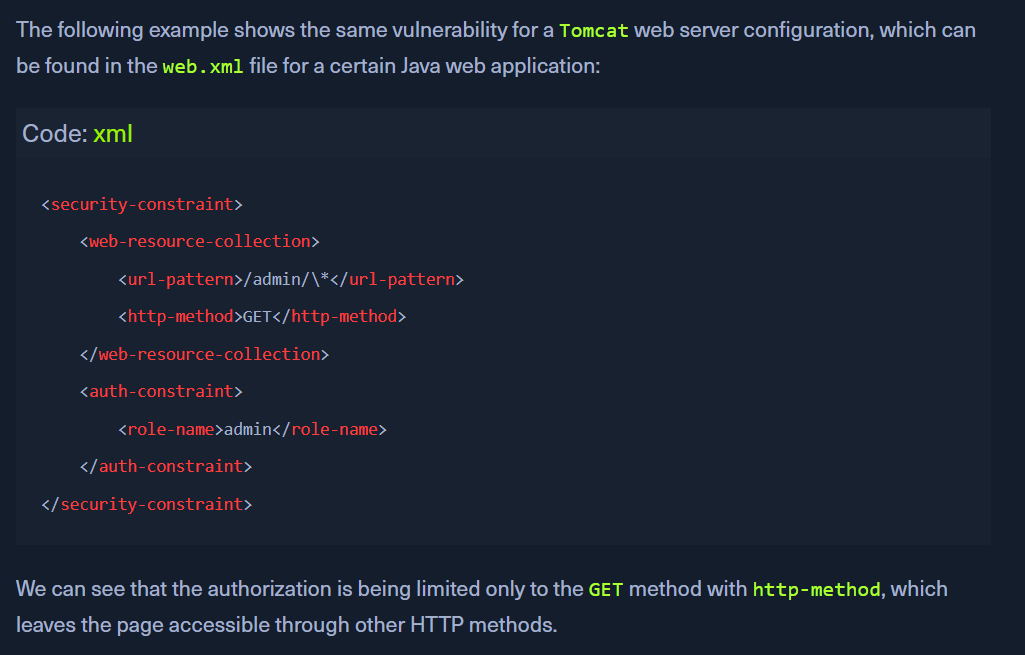
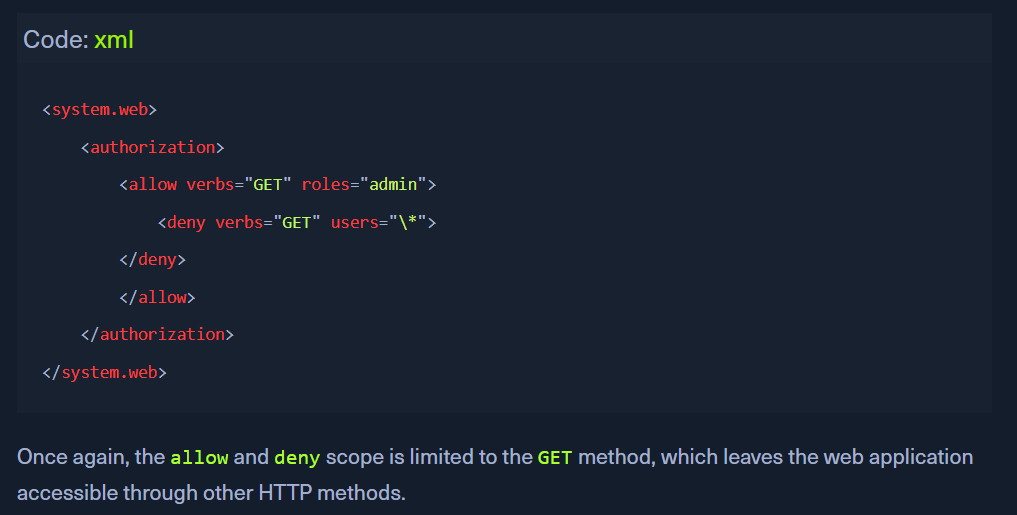
Insecure Config
- the Apache's site configuration file is present in (e.g.
000-default.conf), or in a .htaccess web page configuration file
- For Tomcat:
- For
ASP.NET