Apps connecting to Services
- apps connecting to services can often include connection strings that can be leaked if they are not secured
ELF Executable Examination
- an
octopus_checkerbinary is found on a pentest - running the application locally reveals that it connects to a db instance to check the dbs availability.
- if it trys to connect to a db, it might have some string that has creds
- using https://github.com/longld/peda tools to debug
- using https://github.com/pwndbg/pwndbg & https://pwndbg.re/pwndbg/latest/commands/
DLL File Examination
- DLL file is a
Dynamically Linked Library- it contains code that is called from other programs while they are running - a dll file is found during a pentest
Get-FileMetaData .\MultimasterAPI.dll- says this is
.NETassembly
- says this is
- Using the debugger and .NET assembly editor dnSpy to see the source code directly
- This tool allows reading, editing, and debugging the source code of a .NET assembly (C# and Visual Basic).
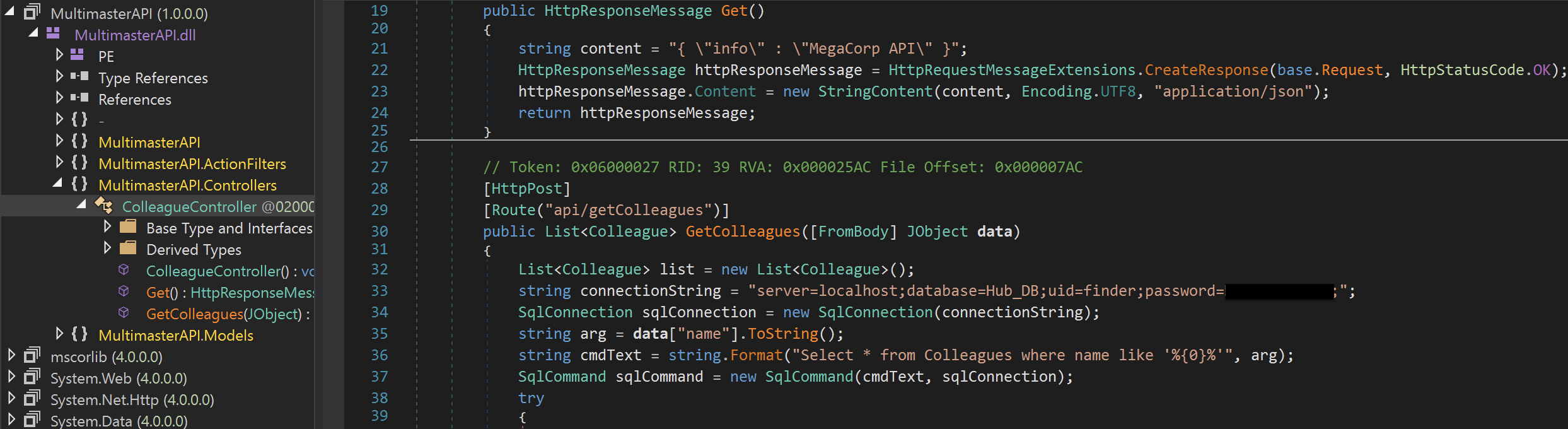
- Inspection of
MultimasterAPI.Controllers->ColleagueControllerreveals a database connection string containing the password.