Identifying filters
Filter/WAF Detection
- If we try our payload and see an error on the same page means that the application has filters in place
- if we saw another page with a
REQUEST-ID, we can say that the WAF blocked it.
- BREAKDOWN
- Payload:
127.0.0.1; whoami
- the filter either detected a blacklisted
character or a command or both
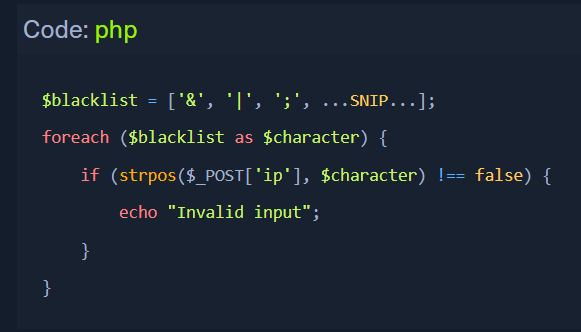
Blacklisted Characters
- eg code:
- if any char in our input string matches, our request is denied.
- we can use
<<< instead of |
Before we start the attempts to bypass a filter, we should try to find the character that is being filtered.
Identifying the Blacklisted character
- Reduce the string to find where the error starts.