Linux - Credentialed
- With valid domain creds, we can get it using: crackmapexec or rpcclient
CRACKMAPEXEC - Get/Pull domain password policy with creds
crackmapexec smb 172.16.5.5 -u avazquez -p Password123 --pass-pol
Netexec
nxc smb 172.16.5.5 -u UserNAme -p 'PASSWORDHERE' --pass-pol
Linux - SMB NULL Session
- Without credentials, use an SMB NULL session or LDAP anonymous bind
- SMB NULL session misconfigs happen when legacy Domain Controllers are updated in place with older configs
- older windows servers allowed anonymous access to certain shares - used for domain enum
- SMB NULL session can be enumerated using enum4linux, CRACKMAPEXEC, rpcclient
RPCCLIENT - to check a DC for SMB Null session access
rpcclient -U "" -N 172.16.5.5- connect to a DCquerydominfo- in the RPC session, query informationgetdompwinfo- get password policy information
enum4linux
- build around samba suite of tools - nmblookup ,net, rpcclient, smbclient

enum4linux -P 172.16.5.5- getting password policyenum4linux-ng -P 172.16.5.5 -oA ilfreight- using ng to export datacat ilfreight.json- displaying output
Linux - LDAP anonymous bind
- This can get a complete listing of users, groups, computers, user account attributes, and the domain password policy
- Legacy setting. New configs require authentication
- Tools -
windapsearch.py,ldapsearch,ad-ldapdomaindump.py
LDAPSearch
ldapsearch -h 172.16.5.5 -x -b "DC=INLANEFREIGHT,DC=LOCAL" -s sub "*" | grep -m 1 -B 10 pwdHistoryLength- getting password policy
Windows
Windows - NULL Sessions
net use \\DC01\ipc$ "" /u:""- DC01 is the host
Other variations
- net use \\DC01\ipc$ "" /u:guest - use some username
- net use \\DC01\ipc$ "password" /u:guest - credentialed
Other:
net.exe
- If we can authenticate into the domain
- tools -
net.exe,PowerView,CrackMapExecported to Windows,SharpMapExec,SharpView net accounts
PowerView
Import-Module .\PowerView.ps1Get-DomainPolicy
INFORMATIKS
pwdPropertiesset to1- Password complexity is enabled on the particular user
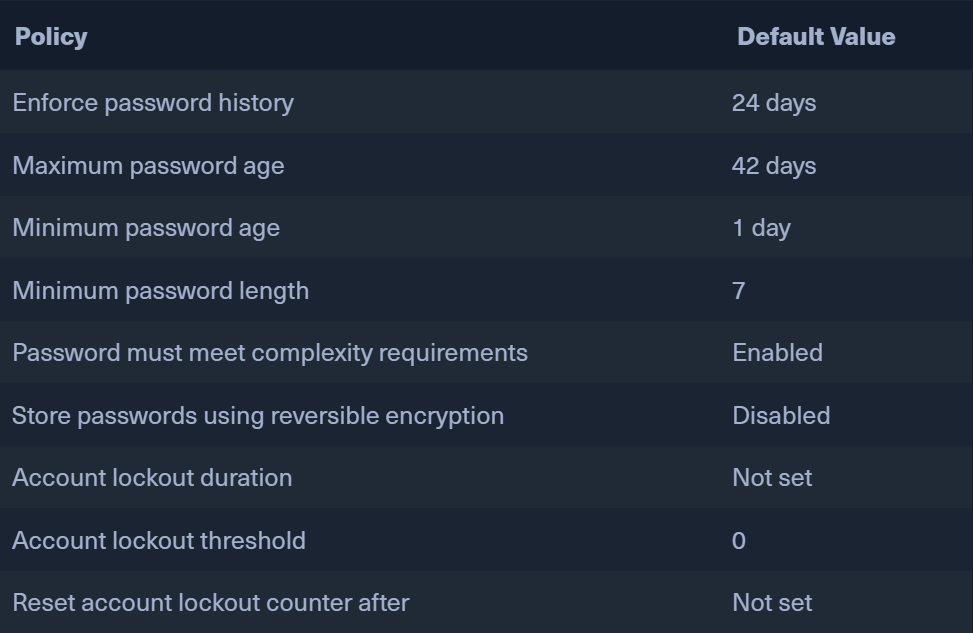
- DEFAULT PASSWORD POLICY when a new domain is created