Stack Based BOF 101
- usually binary files (executables) from c/c++
- Microsoft -
Portable Executable Format (PE) - Unix -
Executable and Linking Format (ELF)- If the linker loads such an executable binary file and the program will be executed, the corresponding program code will be loaded into the main memory and then executed by the CPU.
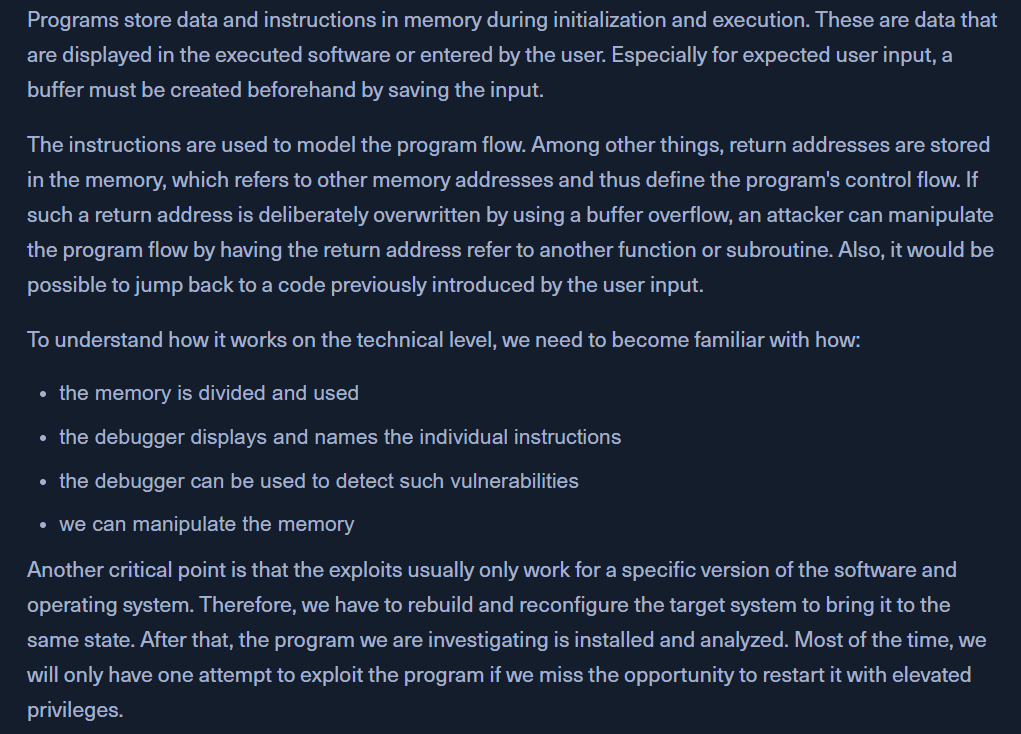
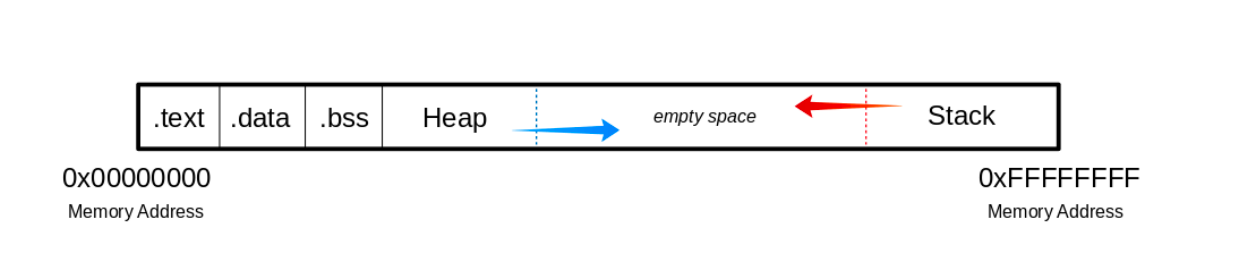
The Memory
- https://www.exploit-db.com/exploits/46763 - freefloat ftp server windows xp
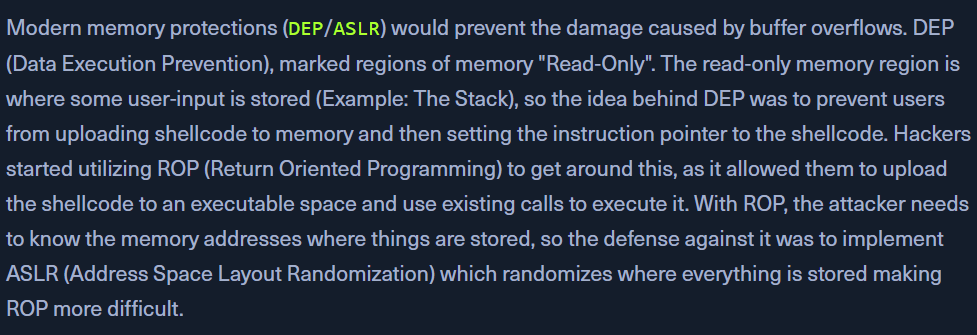
- But, modern systems have
DEP/ASLRto avoid buffer overflow vulnerabilities
Vulnerability
-
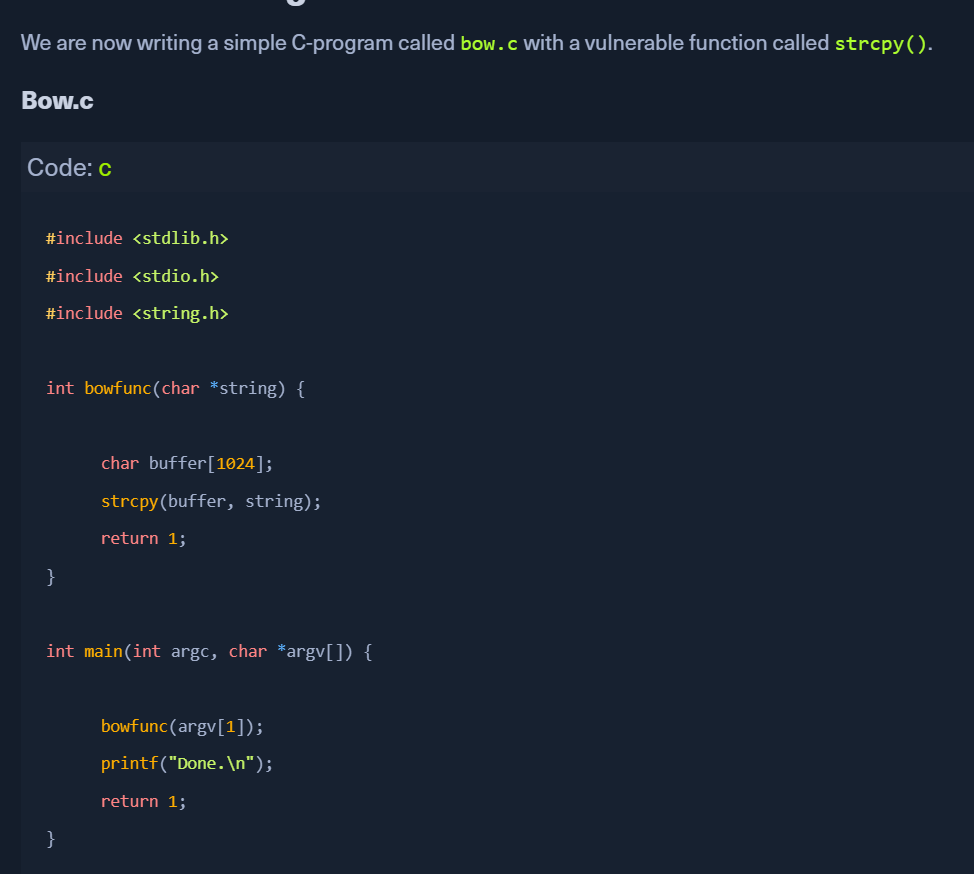
Vulnerable C functions:
strcpygetssprintfscanfstrcat
- C code for
strcpy() - for learning bof, diasable ASLR
- compile the above c code into a 32bit elf binary
GDB
GNU Debugger (GDB)- to view the created binary on the assembler level- provides traceability with breakpoints, stack traces, intervene execution, manipulate variables. call functions independently.
- Once we have executed the binary with
GDB, we can disassemble the program's main function.
GDB AT&T syntax
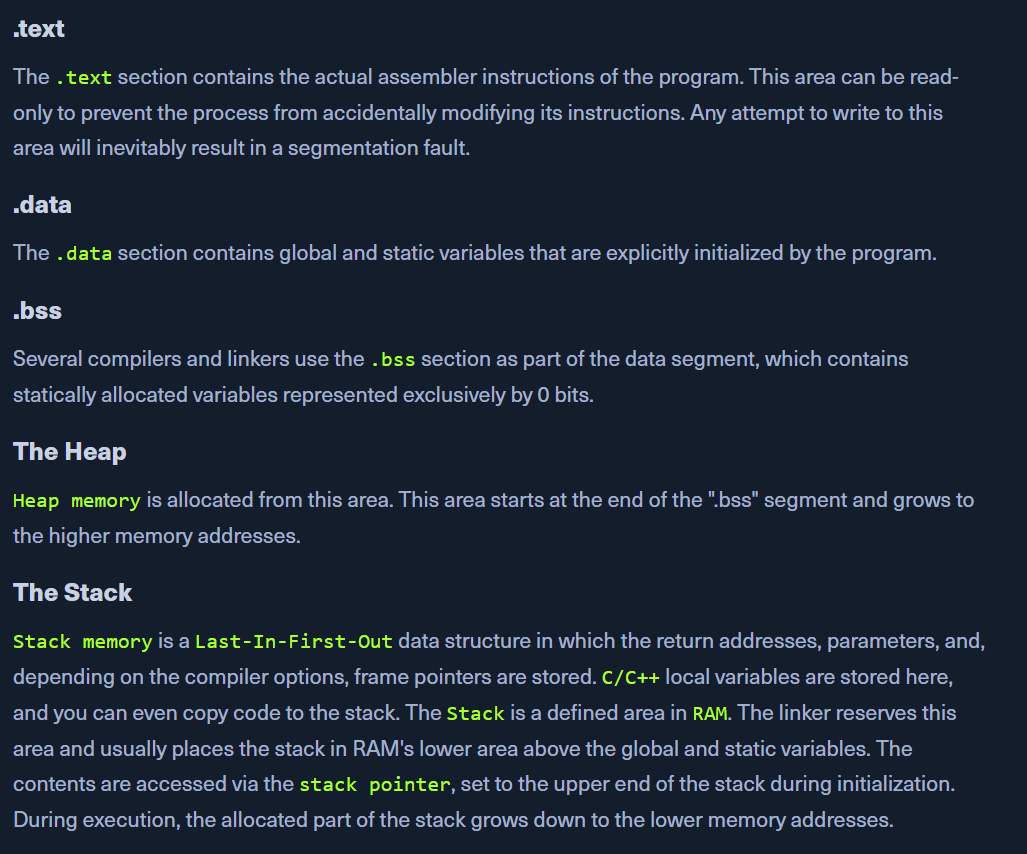
gdb -q bow32disassemble main- starting with the first column:
- hexadecimal numbers -
memory addresses <+4>- address jumps in memory (bytes) based on the respective instruction- assembler instructions - (push, call)
- operations suffixes and their registers (% $ - AT&T syntax)
- hexadecimal numbers -
- instruction | source | destination
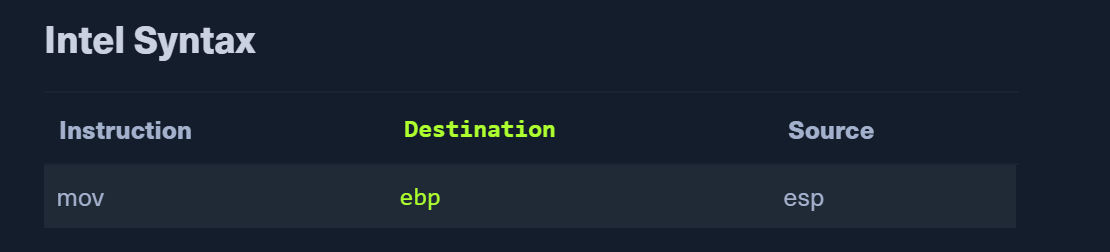
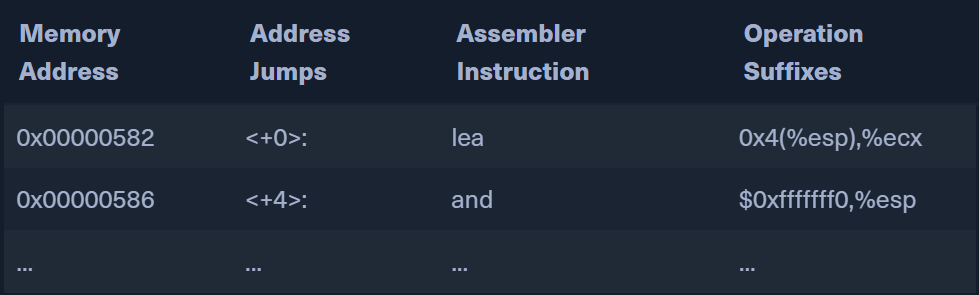
GDB INTEL syntax
- easier to read
- set to default
echo 'set disassembly-flavor intel' >> ~/.gdbinit
- disas with intel syntax
set disassembly-flavor inteldisassemble mainDump of assembler code for function main: 0x00000582 <+0>: lea ecx,[esp+0x4] 0x00000586 <+4>: and esp,0xfffffff0 0x00000589 <+7>: push DWORD PTR [ecx-0x4] 0x0000058c <+10>: push ebp 0x0000058d <+11>: mov ebp,esp 0x0000058f <+13>: push ebx 0x00000590 <+14>: push ecx 0x00000591 <+15>: call 0x450 <__x86.get_pc_thunk.bx> 0x00000596 <+20>: add ebx,0x1a3e 0x0000059c <+26>: mov eax,ecx 0x0000059e <+28>: mov eax,DWORD PTR [eax+0x4] <SNIP>