Bypassing IDOR
- Find parameters that change the output of the app
- use burp intruder to enumerate a given parameter and its response.
Function Disclosure
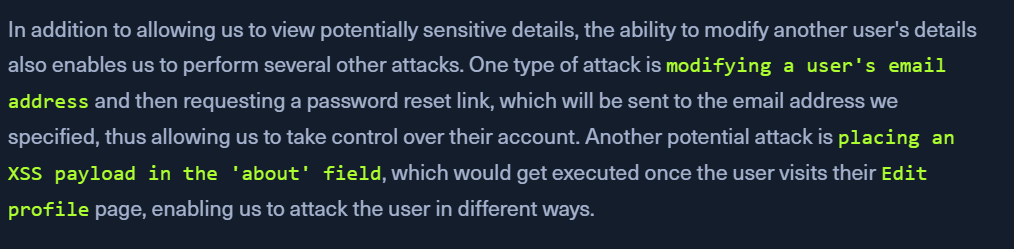
IDOR Information Disclosure Vulnerabilitiesallow us to read various types of resources,IDOR Insecure Function Callsenable us to call APIs or execute functions as another user.