Wildcard Abuse
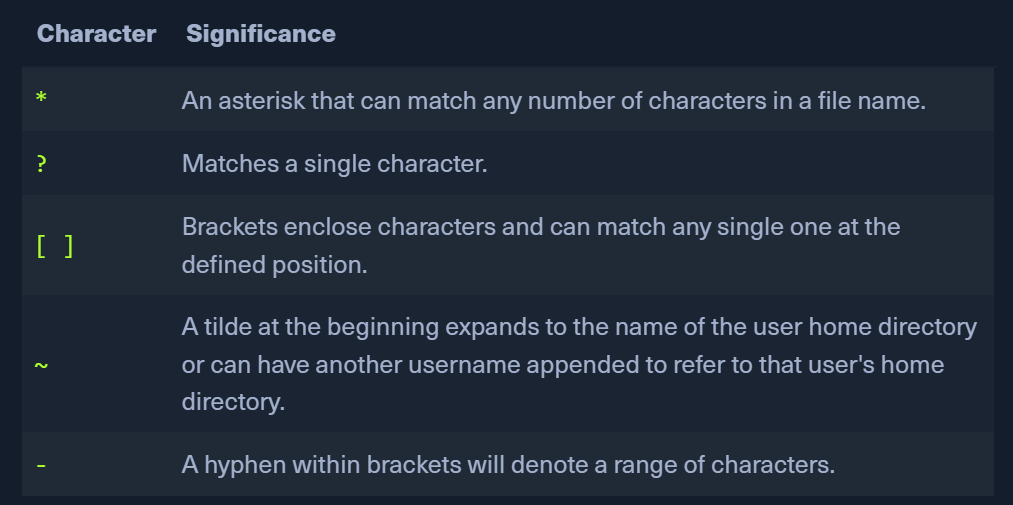
- some characters can be used as a replacement for other characters and the shell will interpret those as valid.
 EXAMPLE
EXAMPLE
TAR file attacks
tarcommand that creates/extracts archives- it takes a command line arg in
--checkpoint-action=arg
- it takes a command line arg in
- Scenario
- We have a cron job that backs up the home folder every minute
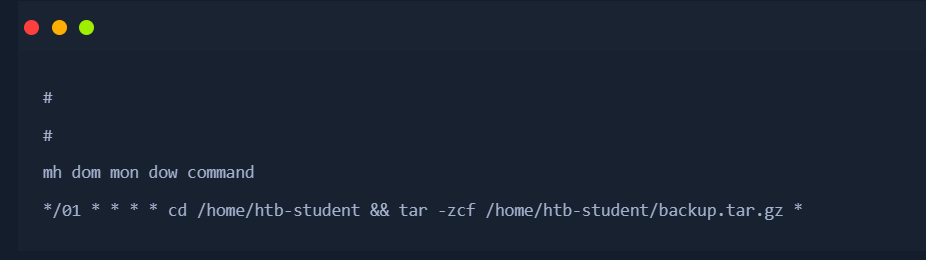
*will be replaced by all the file names in the folder
- we can use it to write commands as file names. when the cronjob runs, these filenames will be interpreted & executed as commands