Steps
- Pre-engagement: Define contract and assessment details
- Info Gathering:
- OSINT - info publicly available on the internet
- Infrastructure Enum
- using OSINT and scans to find servers (mail, name, web), cloud instances
- Service Enum
- id services that allow us to interact with the server
- find the version, information being provided, reason for the service
- Host Enum - find host details based on the infra we've mapped
- Pillaging:
- After Exploiting (i.e. in the Post-Exploitation stage), we look for sensitive information locally
- Vulnerability Assessment:
- Hands on with the information and try to work on an attack vector
- Back and forth with Info Gathering if VA not successful
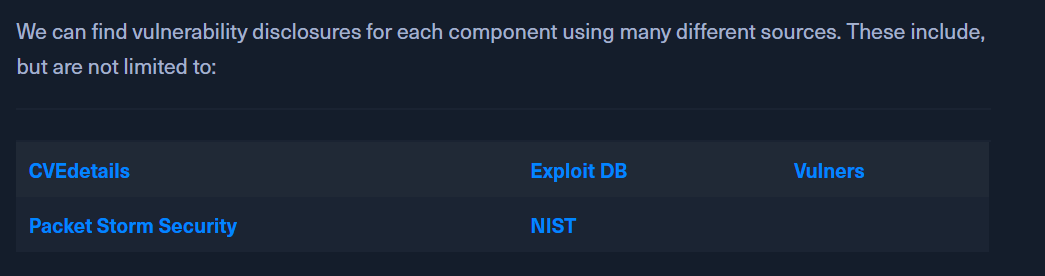
- Analysis of the target to find a vulnerability that can be exploited
- Exploitation:
- Prioritize the vulnerabilities that have been found based on:
- Probability of success
- Complexity
- Probability of Damage
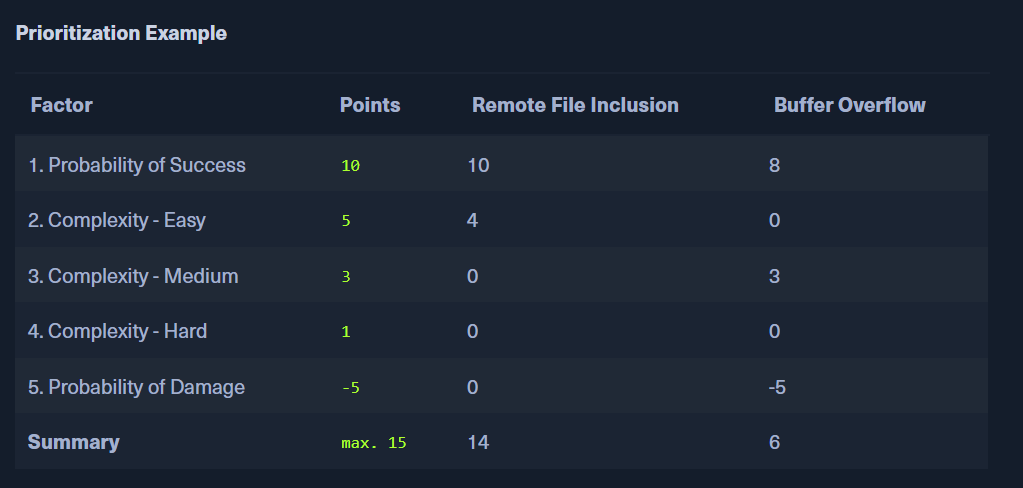
- Prioritize the vulnerabilities that have been found based on:
- Post-Exploitation
- aims to obtain sensitive and security-relevant information from a local perspective and business-relevant information
- might require higher privileges
- Lateral Movement:
- If we have one compromised system in a network, we can use it as a PIVOT to penetrate deeper into the network
- PoC
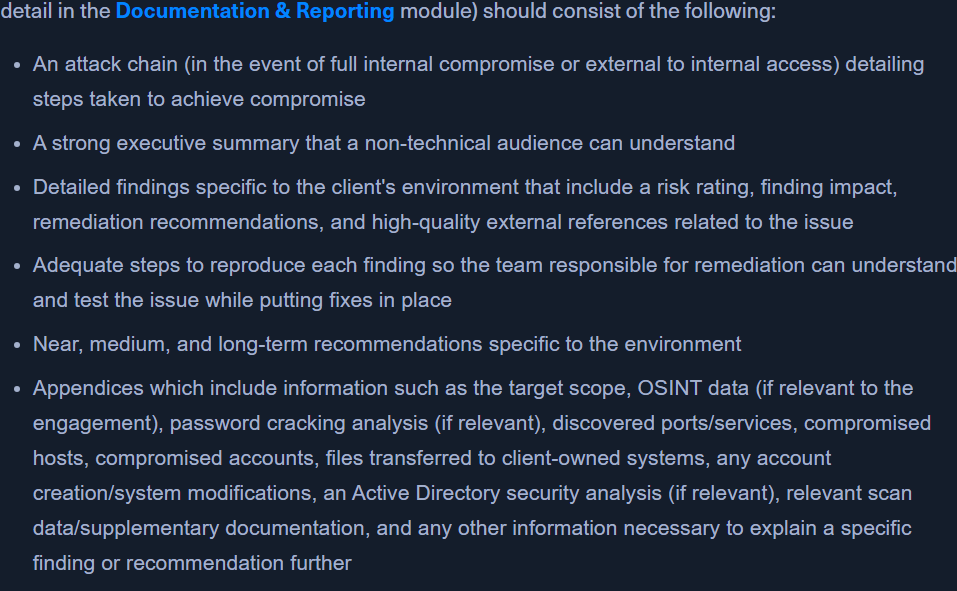
- Post Engagement:
- Clean up our scripts, tools, config changes (minor).
- All our activities must be noted so cleanup is easier
- Document what changes and what we've cleaned
HOW TO APPROACH THIS PATH:
- After 2 modules, HTB will suggest 3 retired machines + 5 active machines that we can work upon. These are single host machines
- 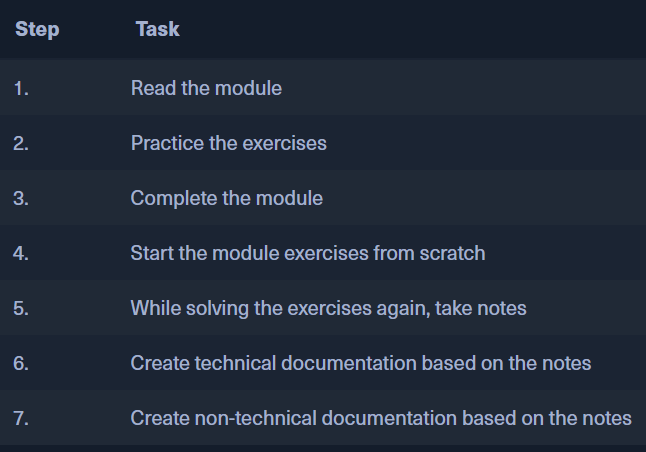 - After reading the module and getting into the machine:
-
- After reading the module and getting into the machine:
- 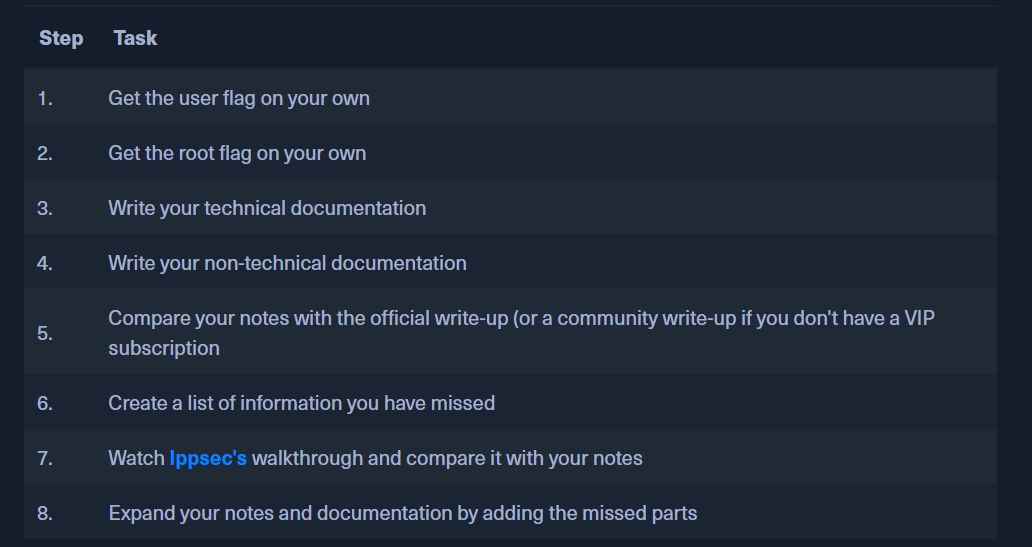 - After this, we can get into Pro Labs and Endgames. These are multi-host machines.
- After this, we can get into Pro Labs and Endgames. These are multi-host machines.