Bypassing Web Application Protections
Anti-CSRF Token Bypass
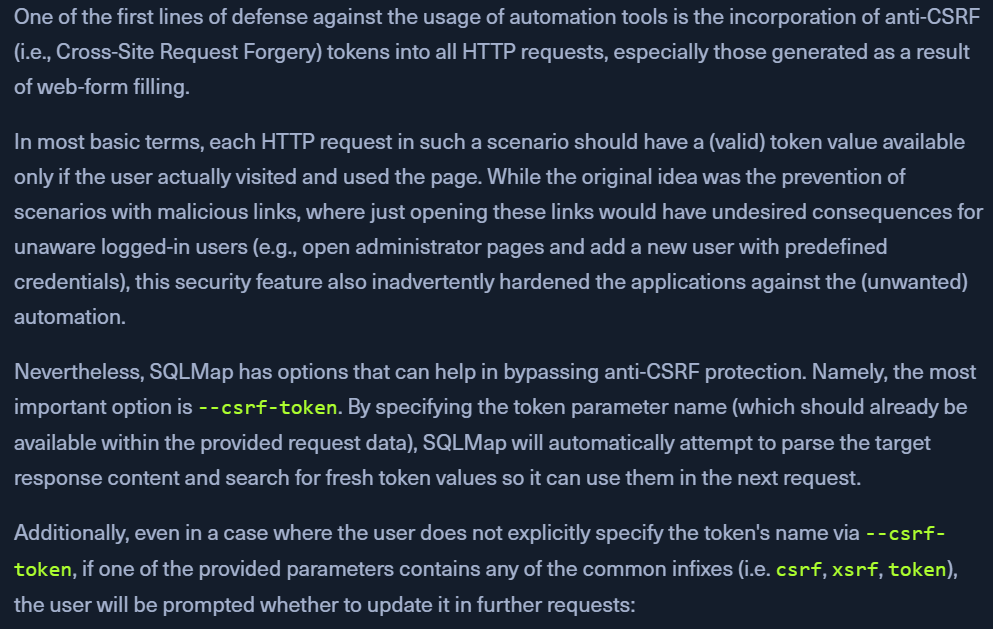
--csrf-tokenwith the parameter name from request data.- SQLMap will parse the response content to get the new csrf token and use it in the consequent responses.
- even if a token name is not provided, sqlmap will prompt for the usual parameters (csrf, xsrf, token)
Usage:
sqlmap -u "http://www.example.com/" --data="id=1&csrf-token=WfF1szMUHhiokx9AHFply5L2xAOfjRkE" --csrf-token="csrf-token"
Unique Value Bypass
- case when web app requires a unique value to be provided inside predefined parameters.
- unlike CSRF there is no need to parse the webpage.
- use
--randomize=<parameter> sqlmap -u "http://www.example.com/?id=1&rp=29125" --randomize=rp --batch -v 5 | grep URI
Calculated Parameter Bypass
- web app expects a proper parameter value to be calculated based on some other parameter value(s).
- eg: h=MD5(id) where
hmust have the hash of another valueid --evalwith a python code can be usedsqlmap -u "http://www.example.com/?id=1&h=c4ca4238a0b923820dcc509a6f75849b" --eval="import hashlib; h=hashlib.md5(id).hexdigest()" --batch -v 5 | grep URI
IP Address Concealing
- if we want to hide our IP or if the webapp is blocking our IP
--proxy="socks4://177.39.187.70:33283where we should add a working proxy- if we have a list of proxies, we can use:
--proxy-file- SQLMap will go sequentially through the list, and in case of any problems (e.g., blacklisting of IP address), it will just skip from current to the next from the list.
- Use
TOR- install tor and there will be a SOCKS4 proxy service at the local port 9050 or 9150.
--check-torto check if the connection is there. Responds with "CONGRATULATIONS"--tor, SQLMap will try to use the local port
WAF Bypass
- SQLMap does this automatically - https://github.com/stamparm/identYwaf
- to skip this step, make it less noisy, we can use
--skip-waf
User-Agent blacklisting bypass
- sqlmap uses
User-agent: sqlmap/1.4.9 (http://sqlmap.org) --random-agent, which changes the default user-agent with a randomly chosen value from a large pool of values used by browsers.
Tamper Scripts
- Tamper scripts are (Python) scripts written for modifying requests just before being sent to the target, in most cases to bypass some protection.
- For example, one of the most popular tamper scripts between is replacing all occurrences of greater than operator (
>) withNOT BETWEEN 0 AND #, and the equals operator (=) withBETWEEN # AND #. This way, many primitive protection mechanisms (focused mostly on preventing XSS attacks) are easily bypassed, at least for SQLi purposes. - Tamper scripts can be chained.
- eg:
--tamper=between,randomcase - sqlmap uses priority to avoid issues.
- some tamper scripts do not change inner content (appendnullbyte)
- eg:
--list-tampersto get all the available tamper scripts- The most notable tamper scripts are the following:
| Tamper-Script | Description |
|---|---|
0eunion |
Replaces instances of UNION with e0UNION |
base64encode |
Base64-encodes all characters in a given payload |
between |
Replaces greater than operator (>) with NOT BETWEEN 0 AND # and equals operator (=) with BETWEEN # AND # |
commalesslimit |
Replaces (MySQL) instances like LIMIT M, N with LIMIT N OFFSET M counterpart |
equaltolike |
Replaces all occurrences of operator equal (=) with LIKE counterpart |
halfversionedmorekeywords |
Adds (MySQL) versioned comment before each keyword |
modsecurityversioned |
Embraces complete query with (MySQL) versioned comment |
modsecurityzeroversioned |
Embraces complete query with (MySQL) zero-versioned comment |
percentage |
Adds a percentage sign (%) in front of each character (e.g. SELECT -> %S%E%L%E%C%T) |
plus2concat |
Replaces plus operator (+) with (MsSQL) function CONCAT() counterpart |
randomcase |
Replaces each keyword character with random case value (e.g. SELECT -> SEleCt) |
space2comment |
Replaces space character ( ) with comments `/ |
space2dash |
Replaces space character ( ) with a dash comment (--) followed by a random string and a new line (\n) |
space2hash |
Replaces (MySQL) instances of space character ( ) with a pound character (#) followed by a random string and a new line (\n) |
space2mssqlblank |
Replaces (MsSQL) instances of space character ( ) with a random blank character from a valid set of alternate characters |
space2plus |
Replaces space character ( ) with plus (+) |
space2randomblank |
Replaces space character ( ) with a random blank character from a valid set of alternate characters |
symboliclogical |
Replaces AND and OR logical operators with their symbolic counterparts (&& and \|) |
versionedkeywords |
Encloses each non-function keyword with (MySQL) versioned comment |
versionedmorekeywords |
Encloses each keyword with (MySQL) versioned comment |
Misc Bypass
--chunked- turns onchunked transfer encodingto split POST requests body into chunks- Blacklisted SQL keywords can be split in chunks to avoid detection.
- The other bypass mechanisms is the
HTTP parameter pollution(HPP), where payloads are split in a similar way as in case of--chunkedbetween different same parameter named values (e.g.?id=1&id=UNION&id=SELECT&id=username,password&id=FROM&id=users...), which are concatenated by the target platform if supporting it (e.g.ASP).