- MAP out the network you know using https://draw.io/
- Allows for documentation and notes for reference
If the exam machine CANNOT ping your attackbox (outbound), use sshuttle for ubuntu and netsh for Windows. If the exam machine CAN ping your attack machine, you can use ligolo.
-
https://posts.specterops.io/offensive-security-guide-to-ssh-tunnels-and-proxies-b525cbd4d4c6
-
Public and Private IPs:
Pivoting
- Move inside the network (where we cant reach from our pwnbox) from one host (we have access to from our pwnbox)
- 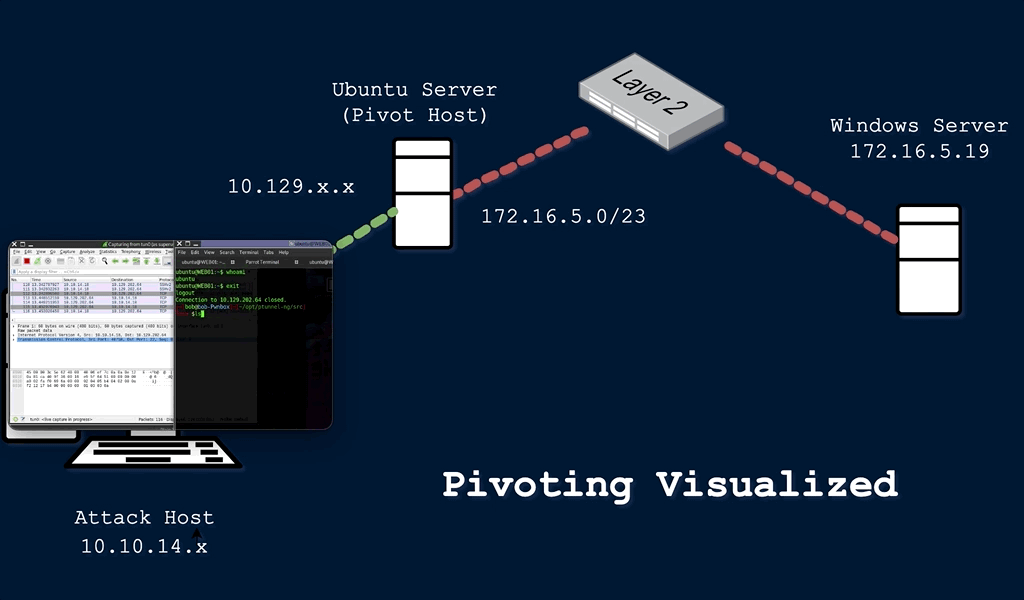 - Move to the Windows server using the Ubuntu server as our Pivot Host
- When landing on a host, check our
- Move to the Windows server using the Ubuntu server as our Pivot Host
- When landing on a host, check our privilege level, network connections, and potential VPN or other remote access software.
- Pivoting is the idea of moving to other networks through a compromised host to find more targets on different network segments.
- Terms used to describe a compromised host that we can use to pivot to a previously unreachable network segment are:
- Pivot Host
- Proxy
- Foothold
- Beach Head system
- Jump Host
Tunneling- subset of pivoting
- create a tunnel that will encapsulate the network traffic into another protocol and route the traffic through it
- only the end users will know about the data
Lateral Movement- further our access to additional hosts, applications, services within a network
- expanding control within an environment
- enables privesc
Networking behind Pivoting
- every computer needs an IP for communication (with or without internet)
- NO IP, NO Communication
- IP either auto assigned by DHCP server
- OR statically assigned:
- Server, Router, Switch virtual interfaces, Printers, any critical service to the network
- OR statically assigned:
- IP is assigned to a NIC (Network Interface controller/card)
- one computer can have multiple NICs (physical or virtual). Hence, multiple IPs
- allows communication on various networks
Commands:
- Linux: ifconfig
- Windows: ipconfig
- We see tun0 interface for our HTB VPN
- This VPN will encrypt traffic and create a tunnel over a public network (internet), through NAT on a public-facing network appliance, and into the internal/private network.
- Subnet mask - https://www.calculator.net/ip-subnet-calculator.html
- When talking to an IP in a different network, the traffic is routed to the device's default gateway
Routing
- make a pivot host route traffic to another network
autoroute
- Reading a routing table on a host
netstat -rip route
- Any traffic destined for networks not present in the routing table will be sent to the
default route
Protocols, Services, Ports
Protocolsare the rules that govern network communicationsprotocols and serviceshave corresponding ports- If IP, means computer reachable over a network
- If open port, means application to connect
- Listening on ports mhanje use ports and protocols that are permitted in the firewall to gain a foothold.