Protected Files
- Mostly files are unencrytped
- List of extensions: https://fileinfo.com/filetypes/encoded
Hunting for files:
for ext in $(echo ".xls .xls* .xltx .csv .od* .doc .doc* .pdf .pot .pot* .pp*");do echo -e "\nFile extension: " $ext; find / -name *$ext 2>/dev/null | grep -v "lib\|fonts\|share\|core" ;done
Hunting for SSH Keys
grep -rnw "PRIVATE KEY" /* 2>/dev/null | grep ":1"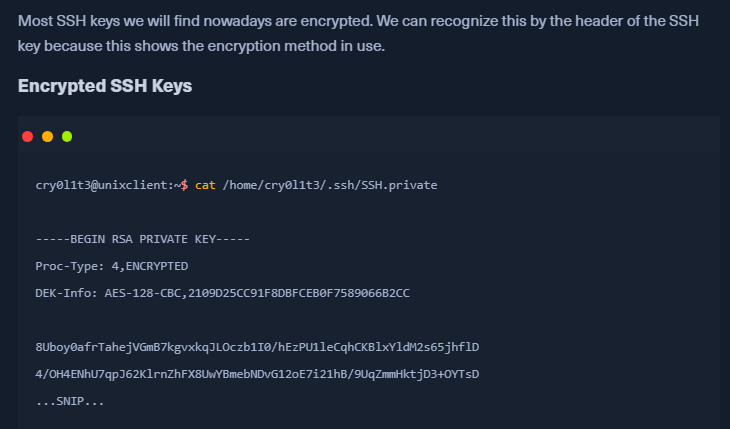
- If SSH key is encrypted, we need to enter a passphrase to decrypt it
- AES_128_CBC can be cracked
Cracking with John
Locate 2john scripts
- locate *2john*
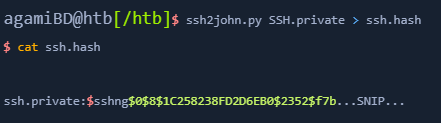
SSH Keys
- For the encrypted ssh keys, we can use
ssh2john.py.- This will store the hash of the encrypted key in a file
- Decrypting the key after you find the password:
openssl rsa -in id_rsa -passin "pass:<crackedpassword>" > id_rsa.decrypted
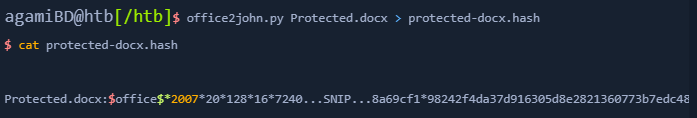
Cracking documents
- If we have a protected docx file, we can use
office2john.py
Cracking PDFs
pdf2john.py