Intro
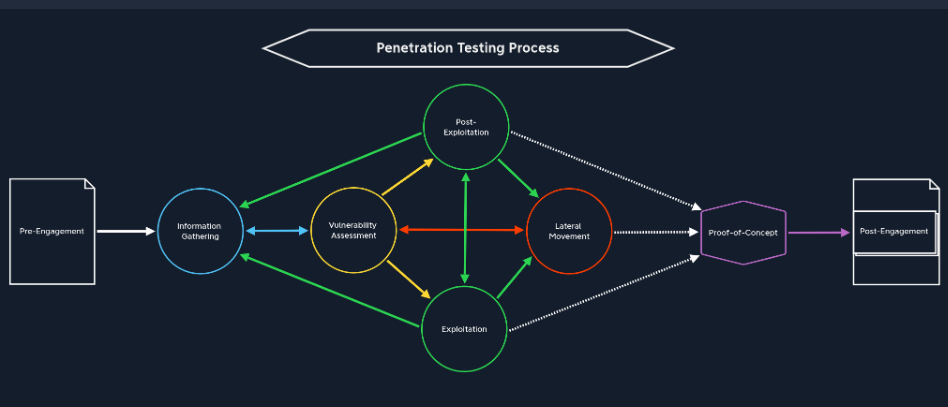
- Pre-Engagement:
- The main commitments, tasks, scope, limitations, and related agreements are documented in writing.
- Info Gathering (RECON):
- ID all the networks and components of the target system
- Vulnerability Assessment:
- use the information found to identify potential weaknesses using scanners or manual analysis
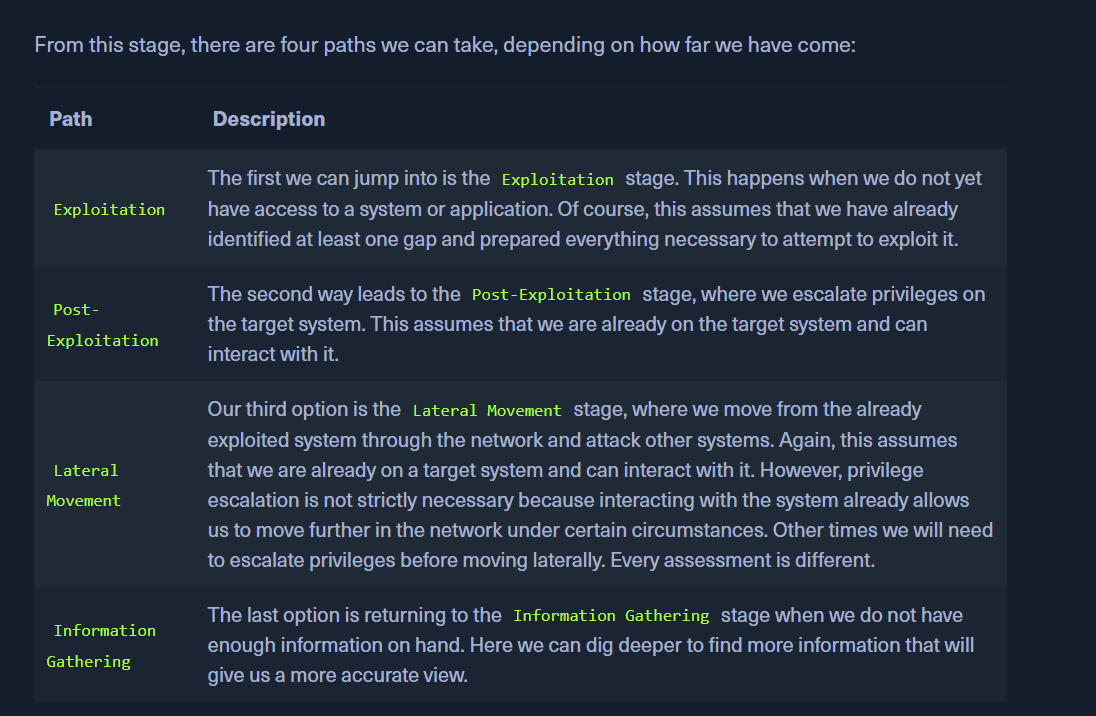
- Exploitation:
- attack performed against a system or application based on the potential vulnerability discovered during our information gathering and enumeration
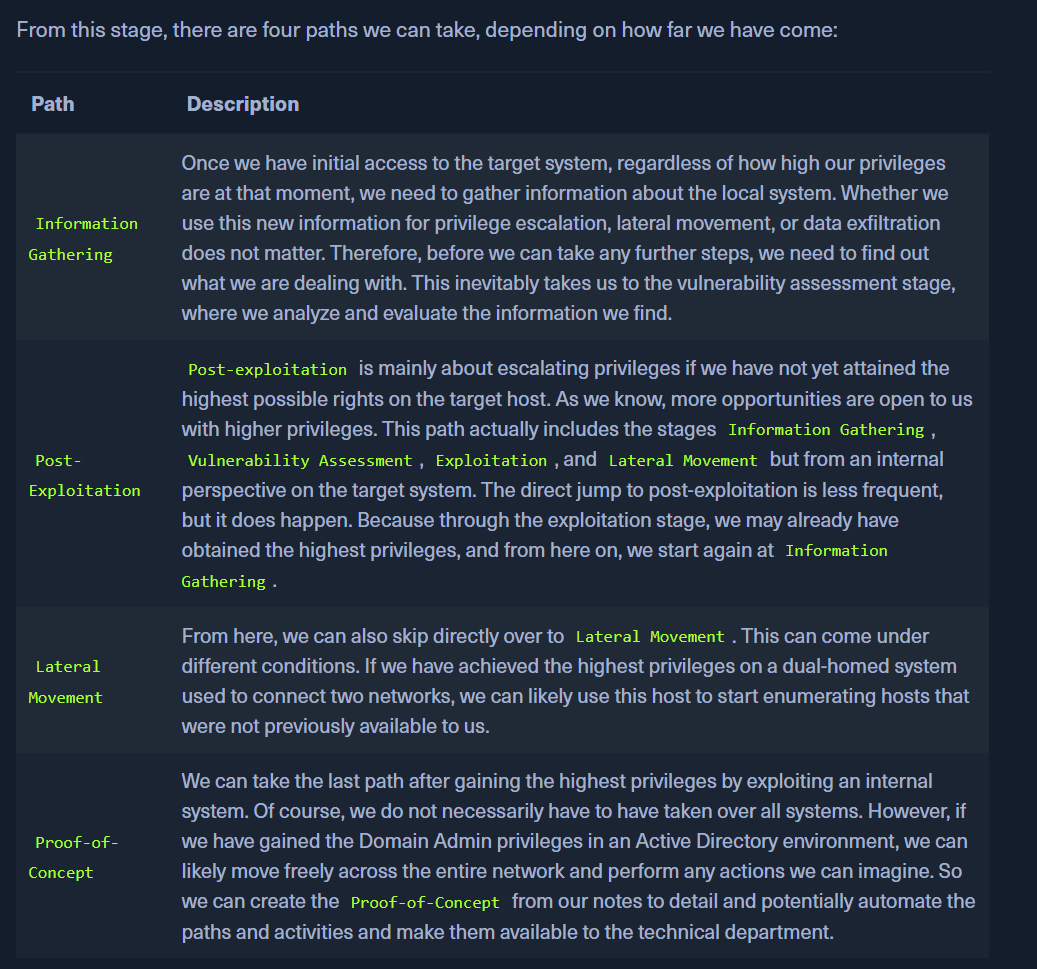
- Post-Exploitation:
- When we attack services and gain access to the system, it is usually a user level access and not root as the services are configured in an isolated way.
- Escalating privileges to the ROOT user is the next step
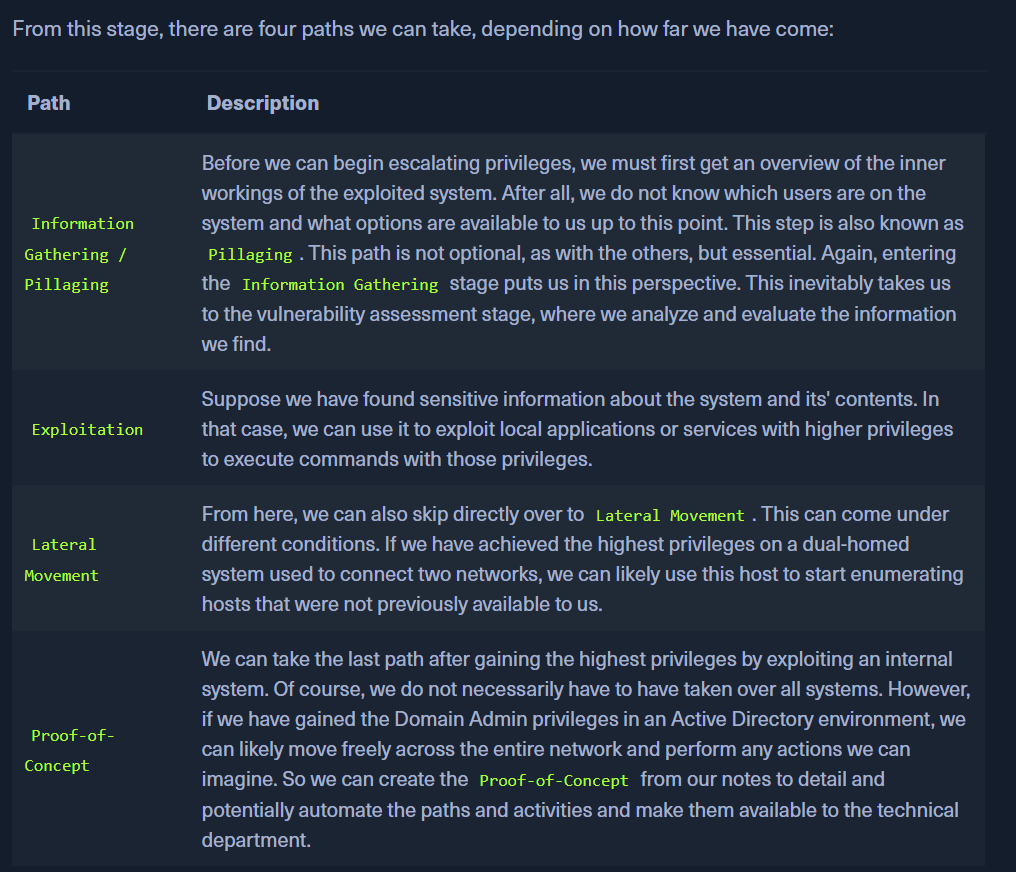
- Lateral Movement:
- Move from one compromised host to another between the subnet.
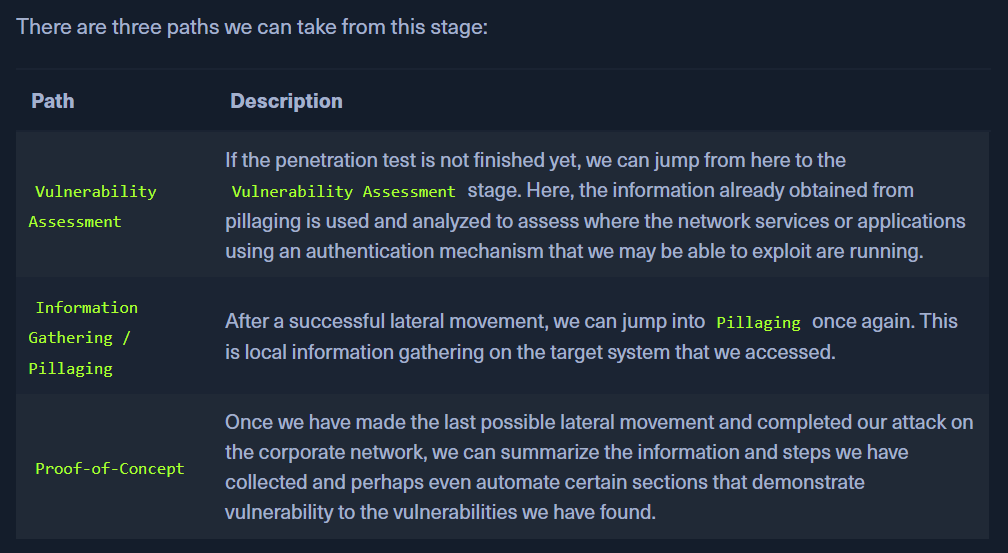
- Proof-of-Concept:
- It is proof that a vulnerability found exists.
- Client will reproduce our finding and confirm it
- Post Engagement:
- optimize and improve documentation and sent it to the customer after review.
- We must also clean up all the exploits and tools left at the target so that they cant be used in the future by other attackers.