Domain Enum
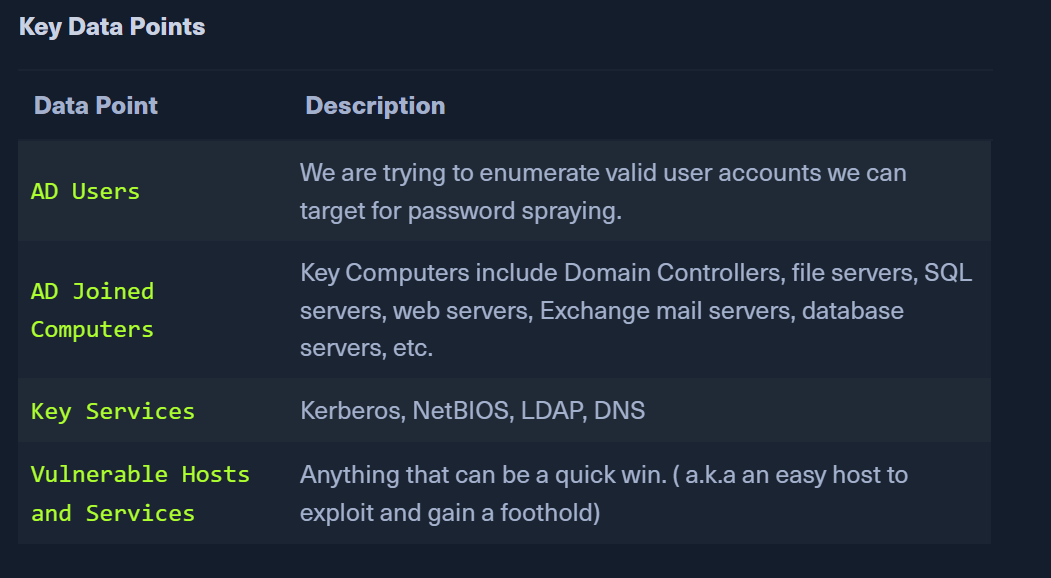
- Jot down Key Data Points
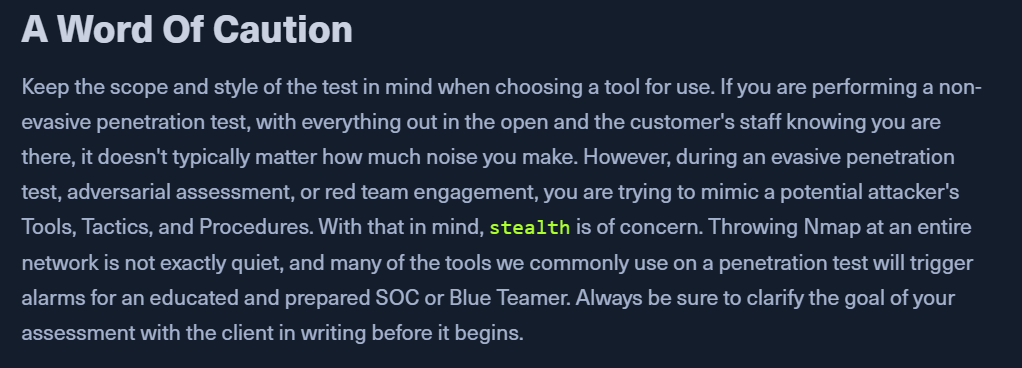
TTPs
- AD is HUGE
- create a game plan to enumerate AD in a progressive way
passiveidentification of any host in the networkactivevalidation to find more about the host (services, names, vulns)- probe the host after validation
Identifying Hosts
Network Sniffing
- "put your ear to the wire" - WIRESHARE or TCPDump
- If no wiresharm
pktmon.exe- windows 10 network monitoring tool- Save PCAP files to analyze them later
Responder
- listen, analyze, poison LLMNR, NBT-NS, MDNS requests and responses.
- Analyze Mode
sudo responder -I ens224 -A
- We might find new hosts not found already using wireshark
- With a few hosts in our bank, we can perform ICMP sweep of the subnet using
fping- https://fping.org/ - can script using fping and uses round-robin to cycle between hosts.
- Ping sweep a network using fping
fping -asgq 172.16.5.0/23
- We get a list of IPs that are up.
NMAP Scanning
- protocols with AD - DNS, SMB, LDAP, Kerberos
- Save the above found ips to hosts.txt
- NMAP to enumerate hosts
sudo nmap -v -A -iL hosts.txt -oN /home/htb-student/Documents/host-enum
Identifying Users
- If the pentest starts without any creds, we need to find a cleartext password or use an NTLM hash for a user account.
- Some foothold is great to open up opps to perform enum and even attacks
Kerbrute - Internal AD Username enum
- https://github.com/ropnop/kerbrute/releases/latest - get a binary
- Kerbrute is silent. Kerberos pre-auth failure is not logged. Used by
Kerbrute -
Use
kerbrutewith the likely usernamesjsmith.txt & jsmith2.txt- https://github.com/insidetrust/statistically-likely-usernames -
Enumerate users using Kerbrute
kerbrute userenum -d INLANEFREIGHT.LOCAL --dc 172.16.5.5 jsmith.txt -o valid_ad_users
- This will output a list of valid usernames
- We can use this list for password spraying
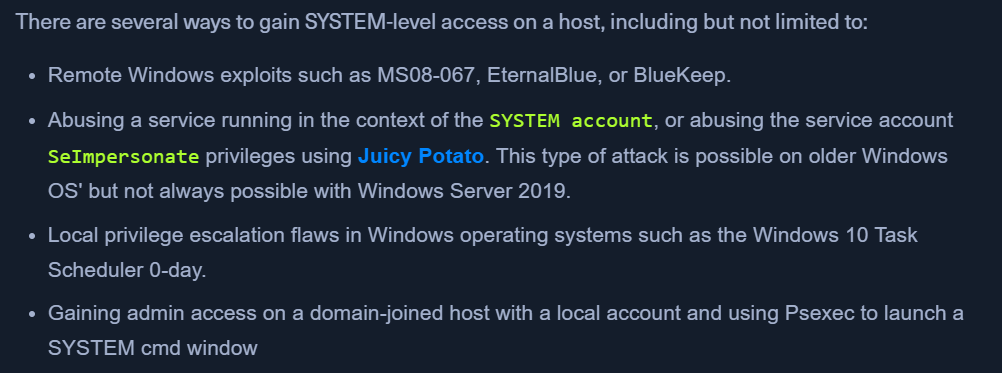
Identifying Potential Vulnerabilities
- NT AUTHORITY\SYSTEM - local system account : has highest access in the OS which is used to run most Windows services
- A
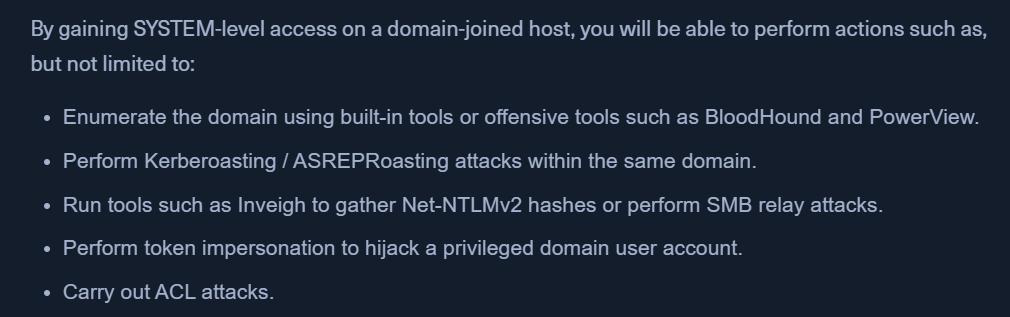
SYSTEMaccount on adomain-joinedhost will be able to enumerate AD by impersonating the computer account (another user account). SYSTEMis likedomain useraccount- GAIN
SYSTEM - USE
SYSTEM